
A Review of Mobile Forensic Investigation Process
Examining a criminal’s phone can reveal a lot of information. For this reason, digital forensics in general and mobile forensics in particular are growing in value as tools for international ...


Digital Forensics Anjali Singhal todayDecember 14, 2023 1

Maintaining the integrity of the evidence is a crucial part of any investigation in the quickly evolving field of technology and the enormous amount of digital data. This principle is unwavering in the field of digital forensics/cyber forensics, which includes retrieving and examining electronic data for legal purposes. Of all the tools available to specialists in digital forensics, one stands out as being particularly crucial to maintaining the credibility of the evidence. -Put Blocker in writing.
In this blog, we will examine write blockers in great detail, explaining their types, features, and the critical role they play in maintaining the reliability of digital evidence.
Write Blockers and Their Use
A hardware tool called a write blocker is intended to stop any writing operations from being carried out on a storage device that is being investigated. To put it simply, it serves as a barrier between the computer used for analysis and the storage device, making sure that only read operations are permitted and that no data is written back to the device. This is an essential function because altering the original data could make it less legitimate and less admissible in court.
What significance do Chain of Custody and Data Integrity have?
Data is the new gold in the digital world. It is extremely valuable in court cases. To preserve its integrity, digital evidence that is gathered for an investigation needs to be handled with extreme caution. The use of write blockers, which stop inadvertent changes to the data, is crucial to this process. Without the right protections, even the most experienced forensic analysts may unintentionally make modifications. Write blockers offer a safe method to stop any unintentional changes, preserving the data’s evidentiary value as digital evidence.
Now here arises, the need of maintaining Chain of Custody along with Data Integrity. So, when we talk about Chain of Custody, it is a critical aspect of any Forensic Investigation. It involves documenting the handling, transfer, and storage of evidence to establish its authenticity and reliability in a court of law and all of which contribute to preserving data integrity.
Every stage of the procedure can be carefully recorded using a write blocker, demonstrating the uninterrupted chain of custody. This paperwork strengthens the evidence’s credibility and dependability by attesting to its passage from the source to the courtroom.
What kinds of Write Blockers are utilized with different types of storage devices?
One should be familiar with the various kinds of storage devices and their interfaces before attempting to comprehend its type. Write Blockers can be classified into various types based on the interfaces of the storage drives. Digital data such as documents, backups, images, videos, apps, and so forth are stored on storage devices. Typical storage device types are:
Hard Disk Drives- SATA, PATA/IDE, SAS
Solid State Drives- NVMe, mSATA, M.2, Blade type SSD
USB Flash Drives- Pen drives/ Thumb Drives
When connecting USB devices or flash drives, Ultrablock USB3 Write Blocker (T8U) is utilized. This device supports non-512B sector sizes and increases imaging speed up to 10X.

Storage devices that use the Ultrablock Forensic Media Card Reader (FMCR) include cards like SDHC, SDXC, MMC, Memory Sticks, and others.
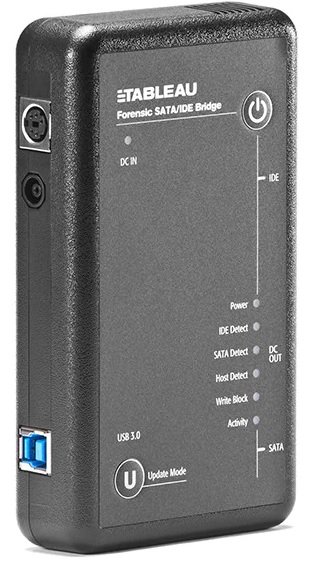
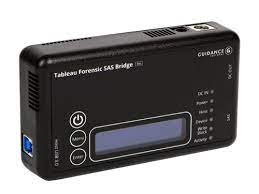
A small hardware write blocker called the UltraBlock SAS Bridge was created expressly to facilitate quick imaging of SAS hard drives. Another name for this is T6U.
PCIe is the Write Blocker (T9U) for SSD storage derives, connecting NVMe, mSATA, and other blade-style SSD drives. When using these specialized Write Blockers, adapters are needed. Without these specialized adapters to connect the SSD drives, investigators are unable to obtain data from the drives.
Next up is a hardware write blocker called Ultra Bay 4P, which is a portable all-in-one tool for connecting storage drives.
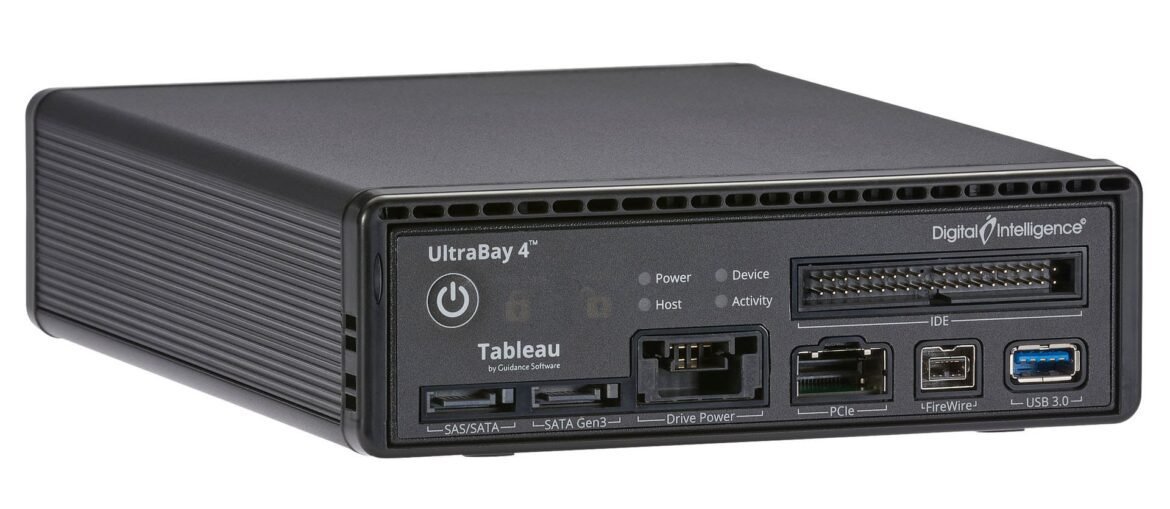
Inbuilt Write Blockers found in FRED Workstations, Duplicators, and Imagers are among the additional Write Blockers. OpenText Tableau’s digital intelligence powers each and every one of these write blockers. Because of the portability of these hardware tools, one can use the Write Blockers at crime scenes for on-the-spot investigations.
The importance of write blockers in the field of digital forensics, where evidence has the power to make or break a case, cannot be emphasized. They are the unsung guardians of data integrity, making sure the truth is kept pure and acceptable in court. Understanding and using write blockers is crucial for maintaining the highest standards of evidence handling and maintaining the credibility of digital investigations, regardless of experience level in the field.
Conclusion
Write blockers are necessary tools in the field of digital forensics, acting as the primary safeguard to maintain the genuineness (integrity) and credibility (authenticity) of digital evidence. By preventing any alterations to the data, writeblockers ensure that the evidence gathered during investigations remains unaltered and retains a reliable chain of custody. In a landscape where digital evidence holds growing importance, write blockers are indispensable tools in protecting truth and supporting the fundamental values of justice.
If this blog has invoked your interest in learning about Digital Forensics, you can explore Hawk Eye Forensic Trainings, a complete guide of Digital Forensic, from setting up the workstation to analyzing key artifacts.
References
Written by: Anjali Singhal
Tagged as: Ultrablock Forensic Media Card Reader, Hawk Eye Forensic, cyber forensic investigation, Write Blocker, Computer Forensic Investigations, Protecting Your Data Integrity, Write Blocker: Protecting Your Data Integrity in the Digital Age, Describe Write Blockers, Chain of Custody, Chain of Custody and Data Integrity, Forensic Investigation, Write Blockers are utilized with different types of storage devices, Ultrablock USB3.

Mobile Forensic Anjali Singhal
Examining a criminal’s phone can reveal a lot of information. For this reason, digital forensics in general and mobile forensics in particular are growing in value as tools for international ...
Copyright 2016-2025 all rights reserved by Hawk Eye Forensic.
Post comments (0)