INTRODUCTION
In today’s digital world, documents are rarely confined to paper. Contracts, agreements, identity proofs, and financial records are frequently scanned, shared, and stored electronically. While this transformation has improved efficiency and accessibility, it has also opened the door to document tampering. At first glance, scanned documents may appear authentic; however, hidden beneath the surface are subtle clues that can reveal manipulation
Understanding the difference between original and scanned documents and how tampering manifests in each is crucial in forensic investigations, legal disputes, and corporate compliance.
Understanding Original vs Scanned Documents
An original document refers to a document created in its primary form, either by hand or digitally, and preserved without alteration. Also, it contains inherent characteristics such as ink flow, pressure patterns, indentation marks, and, in the case of digital originals, metadata.
On the other hand, a scanned document is a digital representation of a physical document. It captures the visual appearance but often loses certain characteristics such as texture, ink depth, and paper quality. This transformation makes scanned documents more vulnerable to manipulation using digital editing tools.
Why Scanned Documents Are More Susceptible to Tampering
Scanned documents are essentially image files in the format of PDF, JPEG, or TIFF. Once digitized, they can be easily manipulated using common editing software. Unlike original documents, where alterations may leave physical traces, this digital tampering can be subtle and hard to detect without forensic analysis.
Common reasons for tampering include:
- financial fraud
- identity manipulation
- contract modification
- academic/professional document falsification.
Because scanned documents lack physical integrity, forensic experts mainly rely on digital traces rather than tactile evidence.
-
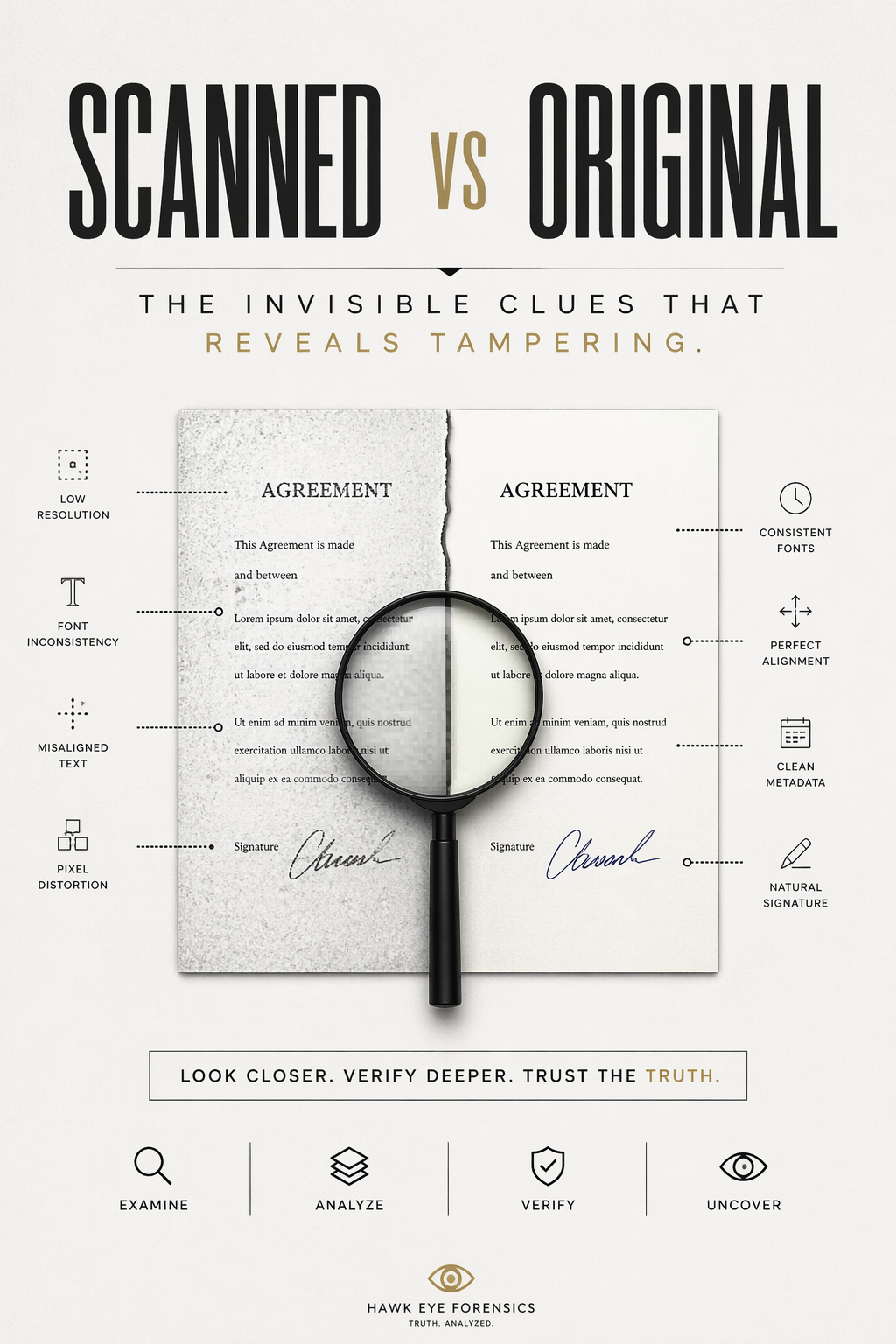
Inconsistent Font and Text Alignment:
One of the most common indicators of tampering is inconsistency in fonts. When text or a line is added or modified digitally, the font type, spacing, or size may vary compared to the original.
Even if the manipulator tries to replicate the font, subtle differences in spacing or baseline alignment can reveal alterations.
-
Pixel Distortion and Resolution Mismatch
A scanned document typically has uniform resolution throughout. When a portion is edited, the modified area may have a different pixel density or compression level. This results in:
- Blurry patches
- Sharper or more pixelated text in certain areas
- Uneven background textures
Zooming into the document often reveals these inconsistencies, which are invisible at normal viewing size.
-
Metadata Discrepancies
Every digital file contains metadata, which records its creation and editing history. In genuine scanned documents, it typically reflects as a single scan event, while tampered files may show:
- multiple editing timestamp
- software editing traces
- inconsistent creation and modification dates.
Metadata analysis is a key forensic method to uncover hidden alterations not visible to the naked eye.
-
Signature Irregularities
Signatures are one of the most targeted elements in document tampering. In scanned documents, signatures are often copied and pasted.
However, such manipulations leave clues like the following:
- Lack of natural variation
- Pixel edges around the signature
- Absence of pressure patterns
In contrast, original signatures show natural ink flow, pressure variation, and stroke order, which are difficult to replicate digitally.
Role of Digital Forensics in Detecting Tampering
Digital forensic experts use advanced tools and methodologies to uncover these invisible clues. Techniques used include:
- Image enhancement and magnification
- Error Level Analysis (ELA)
- Metadata extraction
- Pixel-level comparison
- Signature verification analysis
These methods help reconstruct the history of a document and identify any unauthorised modifications.
Importance in Legal and Corporate Contexts
Document authenticity plays a vital role in courts, financial institutions, and corporate environments. A tampered document can lead to:
- Legal disputes
- Financial losses
- Reputational damage
By identifying whether a document is original or tampered with, forensic experts can help ensure fairness and accountability. Organisations are increasingly relying on forensic analysis to validate documents before making critical decisions.
Best Practices to Prevent Document Tampering
While detection is important, prevention is equally crucial. Some best practices include:
- Using secure document management systems
- Applying digital signatures and encryption
- Maintaining original copies securely
- Avoiding repeated scanning and editing
- Verifying documents through forensic experts when in doubt
Implementing these measures can significantly reduce the risk of tampering.
Conclusion
In conclusion, scanned documents may look similar to originals, but they often carry hidden traces of tampering. From pixel inconsistencies to metadata anomalies, these invisible clues can reveal the truth behind a document’s authenticity. As digital documentation continues to grow, so does the need for vigilance and forensic expertise. Understanding these hidden indicators not only helps in detecting fraud but also strengthens trust in digital systems. In a world where information can be easily altered, this ability to distinguish between scanned and original documents has become more important than ever.


Post comments (0)