Introduction
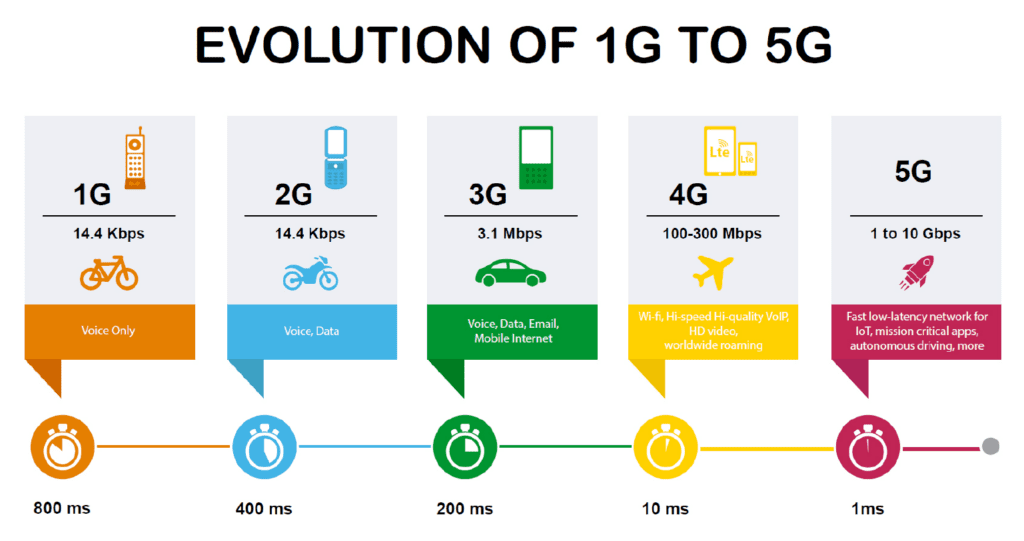
Mobile communication technology has transformed dramatically over the past four decades. From the analog voice calls of the 1G era to the ultra-fast, AI-enabled networks of 5G, every generation of mobile technology introduced not only better connectivity but also stronger security protocols and protection mechanisms.
As mobile phones became central to banking, communication, business, healthcare, and national infrastructure, the need for secure communication grew exponentially. Each generation of mobile technology addressed the vulnerabilities of its predecessor while introducing new cryptographic methods, authentication protocols, and privacy safeguards.
This blog explores the evolution of mobile phone security features and protocols from 1G to 5G.
1G (First Generation) – The Beginning of Mobile Communication
Overview
1G technology emerged in the early 1980s and was based entirely on analog communication systems. Popular standards included:
-
AMPS (Advanced Mobile Phone System)
-
NMT (Nordic Mobile Telephone)
-
TACS (Total Access Communication System)
The primary purpose of 1G was voice communication.
Security Features in 1G
Security in 1G networks was extremely limited because the systems were designed mainly for connectivity rather than protection.
Key Security Characteristics
1. Analog Signal Transmission
2. No Encryption
3. Weak Authentication
4. Device Cloning Vulnerability
Major Security Issues
Significance
Although highly insecure by modern standards, 1G highlighted the urgent need for stronger mobile security frameworks.
2G (Second Generation) – Introduction of Digital Security
Overview
2G technology emerged in the early 1990s and marked the transition from analog to digital communication.
Major standards included:
This generation introduced SMS, digital voice transmission, and significantly improved security.
Security Features in 2G
1. SIM-Based Authentication
2G introduced the Subscriber Identity Module (SIM) card.
The SIM stored:
This allowed secure authentication between the user and network.
2. Encryption Algorithms
GSM introduced encryption algorithms such as:
These algorithms encrypted voice and SMS traffic over the air interface.
3. Challenge-Response Authentication
The network generated a random challenge.
The SIM calculated a response using a secret authentication key.
This reduced cloning attacks significantly.
4. Temporary Mobile Subscriber Identity (TMSI)
Instead of continuously transmitting the IMSI, the network used TMSI to protect user identity.
Security Weaknesses in 2G
Despite improvements, several vulnerabilities existed:
One-Way Authentication
-
The network authenticated the user.
-
The user could not authenticate the network.
-
Fake base stations (IMSI catchers) became possible.
Weak Encryption Algorithms
SMS Vulnerabilities
Importance of 2G Security
2G established the foundation for modern mobile security:
-
SIM-based identity
-
Air-interface encryption
-
Digital authentication
3G (Third Generation) – Stronger Authentication and Data Security
Overview
3G emerged in the early 2000s with high-speed internet access and multimedia capabilities.
Key standards included:
3G introduced mobile internet, video calling, and packet-switched communication.
Security Enhancements in 3G
1. Mutual Authentication
One of the most important upgrades in 3G security.
Now:
This reduced fake tower attacks.
2. AKA Protocol (Authentication and Key Agreement)
The AKA protocol improved authentication and session key generation.
Features included:
-
Integrity protection
-
Secure key exchange
-
Replay attack prevention
3. Stronger Encryption
3G introduced stronger cryptographic algorithms such as:
These improved confidentiality and resistance against interception.
4. Integrity Protection
Unlike 2G, 3G protected signaling messages against tampering.
Security Challenges in 3G
-
Malware attacks increased due to internet access.
-
Smartphones became targets for spyware and phishing.
-
Mobile operating systems introduced application-based risks.
Significance
3G marked the transition from basic telecom security to internet-era cybersecurity.
4G (Fourth Generation) – IP-Based Secure Mobile Ecosystem
Overview
4G technology introduced LTE (Long-Term Evolution) and fully IP-based communication.
This generation enabled:
-
HD video streaming
-
Cloud services
-
Mobile banking
-
VoIP communication
-
IoT integration
Security Features in 4G
1. EPS-AKA Protocol
4G enhanced the AKA mechanism using EPS-AKA (Evolved Packet System Authentication and Key Agreement).
Benefits included:
2. Advanced Encryption Standards
4G used stronger encryption algorithms:
These improved confidentiality and resistance against cryptanalysis.
3. Secure IP Communication
Because LTE was fully IP-based, protocols such as:
4. Improved Subscriber Privacy
Temporary identifiers and secure signaling improved user privacy.
5. Enhanced Roaming Security
Secure inter-network communication reduced roaming fraud risks.
New Security Threats in 4G
IP-Based Attacks
-
DDoS attacks
-
Packet sniffing
-
SIP vulnerabilities
-
DNS attacks
Smartphone Malware
-
Banking trojans
-
Spyware
-
Ransomware
-
Mobile botnets
Application-Level Threats
-
Fake apps
-
Data leakage
-
Weak API security
Importance of 4G Security
4G shifted mobile security toward:
-
Network security
-
Application security
-
Cloud security
-
Endpoint protection
5G (Fifth Generation) – Intelligent and Ultra-Secure Networks
Overview
5G represents the most advanced mobile communication generation.
It enables:
-
Ultra-low latency
-
Massive IoT
-
Smart cities
-
Autonomous vehicles
-
AI integration
-
Industrial automation
Because 5G supports critical infrastructure, security became a top design priority.
Advanced Security Features in 5G
1. SUCI and SUPI Protection
5G protects permanent subscriber identity using:
The identity is encrypted before transmission.
This prevents IMSI catcher attacks.
2. Enhanced Mutual Authentication
5G uses improved authentication mechanisms with stronger cryptographic protections.
3. Service-Based Architecture (SBA) Security
5G uses cloud-native architecture.
Security mechanisms include:
-
API authentication
-
TLS encryption
-
Zero Trust principles
-
Microservice isolation
4. Network Slicing Security
Different virtual networks can operate independently.
Example:
-
One slice for healthcare
-
One for banking
-
One for IoT devices
Each slice can have customized security policies.
5. Stronger Encryption Algorithms
5G employs modern cryptographic techniques with improved key management.
6. Edge Computing Security
Since processing occurs near the user, edge security mechanisms protect:
-
Data confidentiality
-
Low-latency applications
-
IoT communications
7. AI-Based Threat Detection
Artificial intelligence and machine learning help identify:
-
Network anomalies
-
Fraudulent activity
-
Intrusion attempts
-
Malware behavior
Security Challenges in 5G
Despite stronger protections, 5G introduces new risks:
IoT Vulnerabilities
Millions of connected devices increase the attack surface.
Supply Chain Risks
Hardware and software components from multiple vendors can introduce vulnerabilities.
Cloud Security Concerns
Virtualized infrastructure may face:
-
Hypervisor attacks
-
Misconfiguration risks
-
API exploitation
Nation-State Threats
5G infrastructure is considered critical national infrastructure, making it a target for cyber warfare and espionage.
Significance of 5G Security
5G security focuses on:
Comparative Overview of Security Evolution
| Generation |
Security Level |
Authentication |
Encryption |
Major Weakness |
| 1G |
Very Low |
Minimal |
None |
Eavesdropping |
| 2G |
Basic |
SIM-based |
A5 family |
Fake towers |
| 3G |
Moderate |
Mutual authentication |
KASUMI |
Malware growth |
| 4G |
High |
EPS-AKA |
AES/SNOW3G |
IP attacks |
| 5G |
Very High |
Advanced mutual authentication |
Modern cryptography |
IoT complexity |
Role of Mobile Device Security Alongside Network Security
While network security improved generation after generation, smartphone operating systems also evolved.
Key Mobile Device Security Features
Biometric Authentication
-
Fingerprint sensors
-
Face recognition
-
Iris scanning
Secure Enclaves and Trusted Execution Environments
Application Sandboxing
Apps operate in isolated environments.
Mobile Device Management (MDM)
Used in enterprises for:
-
Remote wipe
-
Device monitoring
-
Policy enforcement
End-to-End Encryption
Applications such as messaging platforms introduced E2EE for user privacy.
Future Beyond 5G – Toward 6G Security
Although 6G is still under development, future mobile security may include:
-
Quantum-resistant cryptography
-
AI-native security systems
-
Holographic communication protection
-
Satellite-integrated mobile security
-
Blockchain-based identity management
-
Autonomous cyber defense systems
The focus will increasingly shift toward intelligent, self-healing, and predictive cybersecurity frameworks.
Conclusion
The journey from 1G to 5G reflects a remarkable transformation in mobile communication security.
-
1G had almost no protection.
-
2G introduced digital encryption and SIM authentication.
-
3G strengthened identity verification and integrity protection.
-
4G adopted advanced IP-based security architectures.
-
5G integrated AI, virtualization security, and sophisticated identity protection.
As smartphones continue to dominate personal and professional life, mobile security will remain one of the most critical areas in cybersecurity and digital forensics.
Understanding the evolution of mobile security protocols helps cybersecurity professionals, digital forensic experts, telecom engineers, and law enforcement agencies better analyze threats, investigate cyber incidents, and design secure communication systems for the future.




Post comments (0)