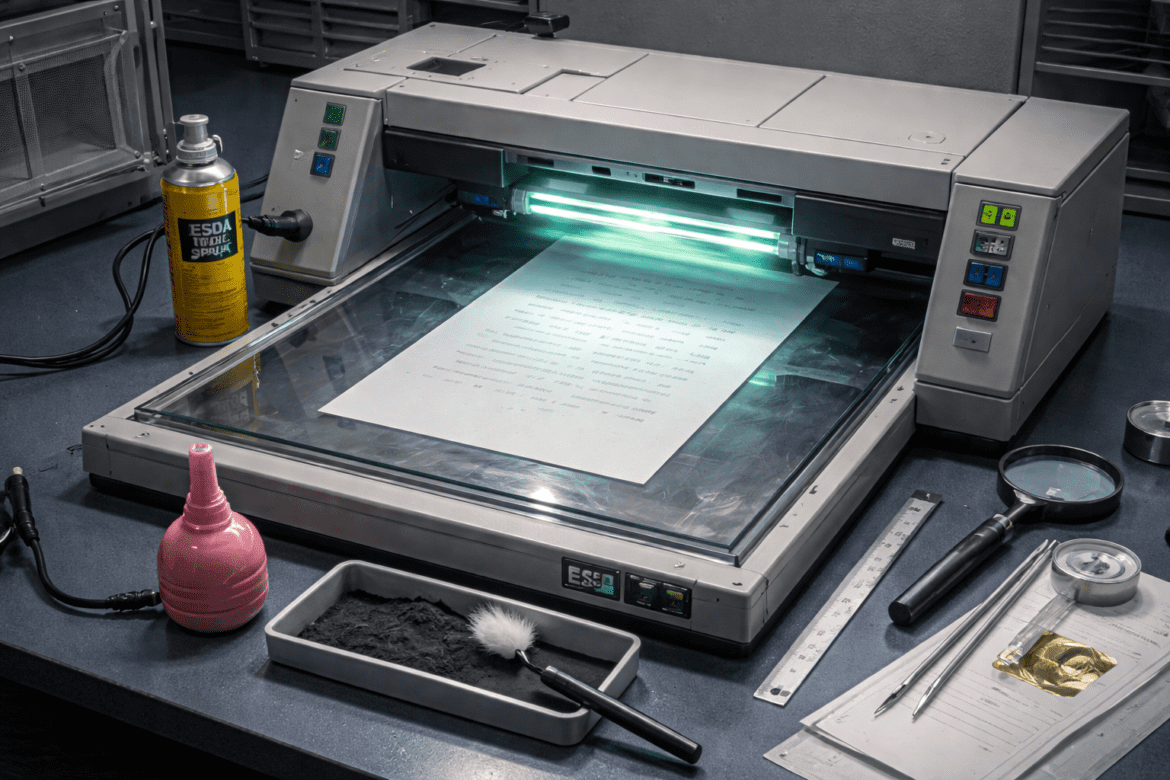
Electrostatic Detection Apparatus (ESDA): How It Reveals Hidden Writing in Forensic Document Examination
In forensic document examination, not all evidence is visible to the naked eye. Sometimes, the most critical information is hidden beneath the surface of a page. This is where the Electrostatic Detection Apparatus, commonly known as ESDA, becomes a powerful investigative tool. ESDA helps forensic experts recover indented writing impressions ...