When a computer is powered off, most investigators focus on hard disks and storage devices. However, one of the most valuable sources of evidence disappears the moment a system shuts down — RAM.
RAM forensics, also known as volatile memory forensics, involves capturing and analyzing data stored in a system’s active memory. In many cybercrime investigations, this volatile data can reveal critical evidence that never gets written to disk.
Understanding RAM forensics is essential in modern digital investigations.
What Is RAM and Why Is It Important?
Random Access Memory (RAM) is the temporary memory a computer uses to run applications, process data, and execute system operations. Unlike hard drives, RAM is volatile, meaning all stored data is lost once power is removed.
However, while the system is running, RAM contains:
In many cases, the most incriminating evidence exists only in RAM.
Why RAM Forensics Matters
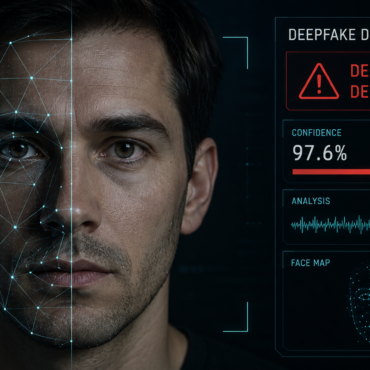
Traditional disk forensics focuses on stored files. However, attackers increasingly use fileless malware, memory-resident tools, and encryption techniques that leave minimal traces on storage devices.
RAM analysis helps investigators:
-
Detect fileless malware
-
Identify malicious processes
-
Extract encryption keys
-
Recover chat sessions or unsaved data
-
Reveal hidden network connections
-
Analyze live system activity
In ransomware investigations, memory analysis may even allow recovery of encryption keys before they disappear.
When Should RAM Be Collected?
RAM must be collected while the system is still powered on. Once shut down, the data is permanently lost.
Therefore, investigators must decide quickly whether to perform:
In cases involving active intrusions, ransomware attacks, or advanced persistent threats, live acquisition is often crucial.
However, performing live analysis requires expertise, because interacting with the system may alter data. Proper documentation and validated tools are essential.
How RAM Is Acquired
RAM acquisition involves creating a memory dump — a complete snapshot of the system’s active memory at a specific time.
Common tools used in memory acquisition include:
The output is typically a .raw or .mem file, which can then be analyzed using forensic frameworks.
RAM Analysis Tools
After acquisition, investigators analyze the memory dump using specialized tools such as:
These tools help extract structured artifacts including:
-
Running process lists
-
DLL files
-
Registry data
-
Network sessions
-
Injected code
-
Suspicious handles
Memory analysis often reveals artifacts that never appear in disk analysis.
Challenges in RAM Forensics
Despite its importance, RAM forensics presents several challenges:
First, volatility — data disappears instantly when power is lost.
Second, size — modern systems may contain 16GB, 32GB, or more memory, making analysis time-consuming.
Third, encryption and obfuscation — advanced malware hides itself inside legitimate processes.
Fourth, legal concerns — live acquisition may raise procedural and documentation issues.
Because of these challenges, investigators must be trained and follow standardized forensic procedures.
Legal and Evidentiary Considerations
Courts require investigators to demonstrate:
Since RAM acquisition modifies the running system slightly, documentation becomes even more critical.
Transparency and reproducibility strengthen admissibility.
Conclusion
RAM forensics has become indispensable in modern cyber investigations. As attackers adopt fileless techniques and memory-resident malware, volatile memory often holds the most revealing evidence.
While disk forensics tells us what was stored, RAM forensics tells us what was happening.
In digital investigations, timing is everything — and when it comes to volatile memory, seconds can mean the difference between critical evidence recovered and evidence lost forever.



Post comments (0)