Smartphone brands today have made fingerprint unlocking feel almost effortless—you just tap or rest your finger, and you’re in. Whether the sensor is placed on the front, back, or hidden under the display, it’s all about making access fast without compromising accuracy.
But here’s something most people don’t realise: your phone isn’t actually saving a picture of your fingerprint. Instead, it converts your fingerprint into a unique digital code—a kind of mathematical pattern that represents the key features of your print. This data is then stored in highly secure areas within the device, such as a Trusted Execution Environment (TEE) or Secure Enclave, designed specifically to keep sensitive information safe and isolated from the rest of the system.
Security Advantages of Fingerprint Authentication
The popularity of fingerprint biometrics stems from its multiple security benefits:
- Uniqueness and Permanence: No two individuals share the same fingerprints, not even identical twins. This makes fingerprint authentication highly reliable.
- Convenience: Users can unlock devices instantly without remembering complex passwords.
- Reduced Risk of Password Theft: Unlike PINs or passwords, fingerprints cannot be easily shared, observed, or phished.
- Multi-Factor Integration: Fingerprints can be combined with other authentication methods to strengthen security.
These advantages have made fingerprint biometrics a standard feature in smartphones, enhancing user trust and adoption globally.
Security Limitations and Vulnerabilities
Despite its strengths, fingerprint authentication is not foolproof. Several vulnerabilities have been identified:
- Spoofing Attacks: Researchers have demonstrated that fingerprint sensors can sometimes be deceived using artificial fingerprints made from materials like silicone or gelatin.
- Residual Prints: Latent fingerprints left on the screen or sensor can potentially be lifted and reused.
- Hardware Limitations: Lower-end sensors may lack the precision required to distinguish between genuine and fake prints.
- Irreplaceability: Unlike passwords, fingerprints cannot be changed if compromised. Once leaked, the risk is permanent.
These limitations highlight that while fingerprint biometrics enhances security, it should not be considered a standalone solution.
Forensic Challenges in Fingerprint-Protected Devices
From a forensic perspective, fingerprint-enabled smartphones present significant challenges for investigators and digital forensic experts.
- Restricted Access to Evidence: Fingerprint locks can prevent investigators from accessing crucial data during an investigation. Unlike passwords, which can sometimes be cracked or bypassed using forensic tools, biometric locks are tied directly to the user’s physical identity.
- Legal and Ethical Concerns: The use of fingerprints to unlock devices raises complex legal questions. In many jurisdictions, compelling an individual to provide a fingerprint may be treated differently from forcing them to disclose a password. This creates ambiguity in legal procedures and evidence admissibility.
- Secure Storage Mechanisms: Modern smartphones store fingerprint templates in secure hardware zones, making it extremely difficult to extract or tamper with the data. While this enhances user security, it limits forensic access and analysis.
- Live vs. Dead Fingerprint Issue: Some advanced devices incorporate liveness detection to ensure that the fingerprint is from a living individual. This adds another layer of complexity for forensic experts attempting to access locked devices.
- Data Volatility: In many cases, repeated failed attempts or certain triggers (such as device reboot) can disable fingerprint access, reverting to passcode-only mode. This can hinder timely evidence acquisition.
Bridging the Gap: Security vs Forensics
The conflict between user privacy and forensic accessibility is at the heart of this issue. Smartphone manufacturers prioritise user data protection, often implementing strong encryption and secure biometric systems. On the other hand, forensic investigators require lawful access to digital evidence to solve crimes.
To bridge this gap, several approaches are being explored:
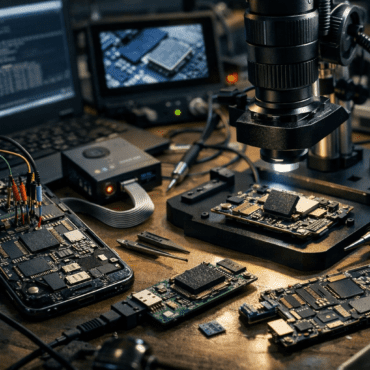
- Advanced Forensic Tools: Development of sophisticated tools capable of bypassing or analysing locked devices without compromising data integrity.
- Legal Frameworks: Clear guidelines on the use of biometric data in investigations can help balance privacy rights and law enforcement needs.
- User Awareness: Educating users about combining biometrics with strong passcodes can improve both security and forensic feasibility.
Conclusion
Fingerprint biometrics in smartphones represents a significant leap in personal security, offering a seamless blend of convenience and protection. However, it is not without its flaws. From spoofing risks to forensic access challenges, this technology sits at the intersection of innovation and complexity.
For digital forensic professionals, the rise of biometric security demands continuous adaptation and expertise. As technology evolves, so must the methods used to investigate and interpret digital evidence. Ultimately, achieving a balance between robust security and lawful forensic access remains one of the most critical challenges in the modern digital landscape.

Post comments (0)