IoT Forensics: Evidence from Smart Homes & Wearables
The rapid growth of Internet of Things (IoT) technology has changed the way people interact with their surroundings. Smart homes and wearable devices now record daily activities, movements, and interactions in real time. As a result, these devices have become valuable sources of digital evidence in modern forensic investigations.
Today, investigators no longer rely only on computers and smartphones. Instead, they increasingly examine smart speakers, fitness trackers, CCTV cameras, and connected home systems. This blog explains how IoT forensics works, what evidence smart homes and wearables provide, and why this data matters in legal investigations.
What Is IoT Forensics?
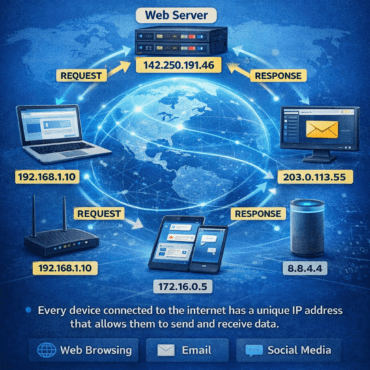
IoT forensics focuses on identifying, collecting, and analyzing data generated by internet-connected devices. Unlike traditional digital devices, IoT systems often store data across multiple locations. For example, information may exist on the device itself, a companion mobile application, or a cloud server.
Therefore, forensic experts must examine multiple data sources simultaneously to reconstruct events accurately. This distributed nature makes IoT forensics complex, but it also increases its evidentiary value.
Smart Homes as Silent Digital Witnesses
Smart homes continuously record user interactions. Consequently, they often act as silent witnesses during investigations.
Common smart home devices examined in forensic cases include:
-
Smart door locks
-
Smart speakers and voice assistants
-
CCTV cameras and video doorbells
-
Smart lighting systems and thermostats
-
Home automation hubs
These devices generate detailed logs that record time, user actions, and system responses.
For example, a smart door lock can show when a door was unlocked and whether access occurred remotely. Similarly, smart cameras can provide motion-triggered recordings and timestamps. As a result, investigators can establish timelines with greater accuracy.
Wearable Devices as Personal Evidence Sources
Wearable devices such as smartwatches and fitness bands collect highly personal data. Unlike phones, wearables track physical activity continuously. Therefore, they often provide precise time-based evidence.
Wearable devices can reveal:
-
Step counts and movement patterns
-
Heart rate and sleep activity
-
GPS routes and location history
-
Activity start and stop times
For instance, step data can confirm whether a person was active or stationary at a specific time. Similarly, GPS logs can support or contradict alibi statements. Because of this, wearables frequently play a crucial role in criminal and civil investigations.
Cloud Data and Its Forensic Importance
Most IoT devices rely heavily on cloud services. Even when investigators cannot access the physical device, cloud data may still exist.
Cloud-stored evidence often includes:
Therefore, forensic experts frequently combine device data and cloud data to obtain a complete picture. However, investigators must always follow legal procedures while accessing cloud-based evidence.
Key Challenges in IoT Forensics
Despite its value, IoT forensics presents several challenges.
First, data fragmentation complicates investigations. Evidence may exist across devices, routers, smartphones, and cloud servers.
Second, limited storage affects data retention. Many IoT devices overwrite old data quickly, which reduces the available forensic window.
Third, proprietary systems restrict access. Manufacturers often use closed operating systems and non-standard data formats.
Additionally, encryption and strong security controls can limit direct access to stored information. As a result, early forensic intervention becomes essential.
Forensic Methodology for IoT Investigations
Investigators must follow a structured approach to handle IoT evidence effectively.
-
Identification – Investigators identify all IoT devices connected to the environment.
-
Preservation – They secure devices and prevent data overwriting or remote access.
-
Collection – Experts collect data from devices, mobile apps, routers, and cloud accounts.
-
Analysis – They correlate logs, timestamps, and activity records.
-
Documentation – Proper documentation ensures chain of custody and legal admissibility.
Because IoT data can change rapidly, timely action significantly improves evidence quality.
Legal Value of IoT Evidence
Courts increasingly accept IoT-generated data when experts demonstrate authenticity and integrity. Moreover, clear documentation and expert interpretation strengthen evidentiary value.
IoT evidence has supported cases involving:
Therefore, IoT forensics now plays a critical role in modern legal proceedings.
The Future of IoT Forensics
As smart cities, connected vehicles, and health-monitoring systems expand, IoT forensics will grow further. In the future, investigators will rely more on automation, artificial intelligence, and standardized forensic frameworks to handle large data volumes.
Consequently, professionals who understand IoT ecosystems will remain in high demand.
Conclusion
IoT devices do far more than automate daily life. They record detailed, time-stamped digital footprints that can clarify events and support investigations. Smart homes and wearable devices now serve as powerful sources of forensic evidence.
When experts preserve and analyze this data correctly, IoT forensics bridges the gap between physical and digital evidence. Ultimately, it helps investigators uncover facts, verify timelines, and support justice with scientific accuracy.


Post comments (0)