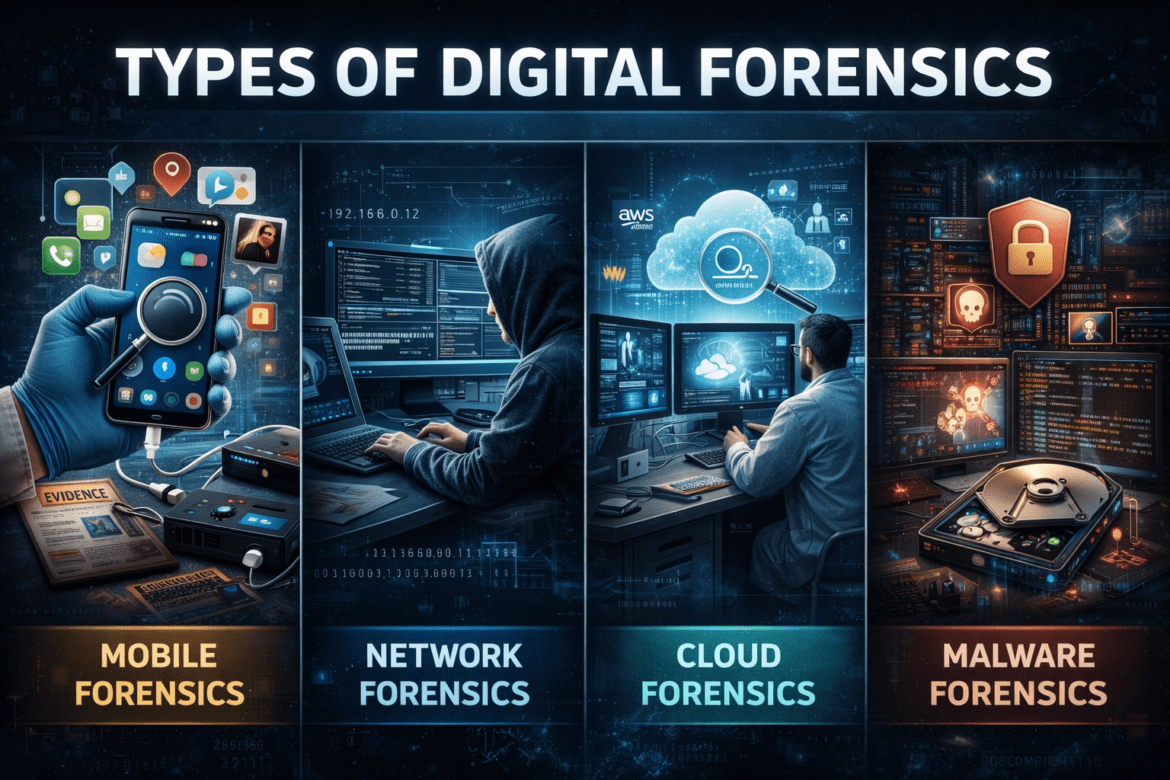
Types of Digital Forensics: Mobile, Network, Cloud, Malware Explained
Introduction In today’s digital world, cybercrimes are increasing rapidly, making digital forensics an essential part of modern investigations. From smartphones to cloud servers, digital evidence is everywhere. Understanding the types of digital forensics helps investigators analyze, recover, and preserve crucial data that can solve crimes, prevent fraud, and support legal ...