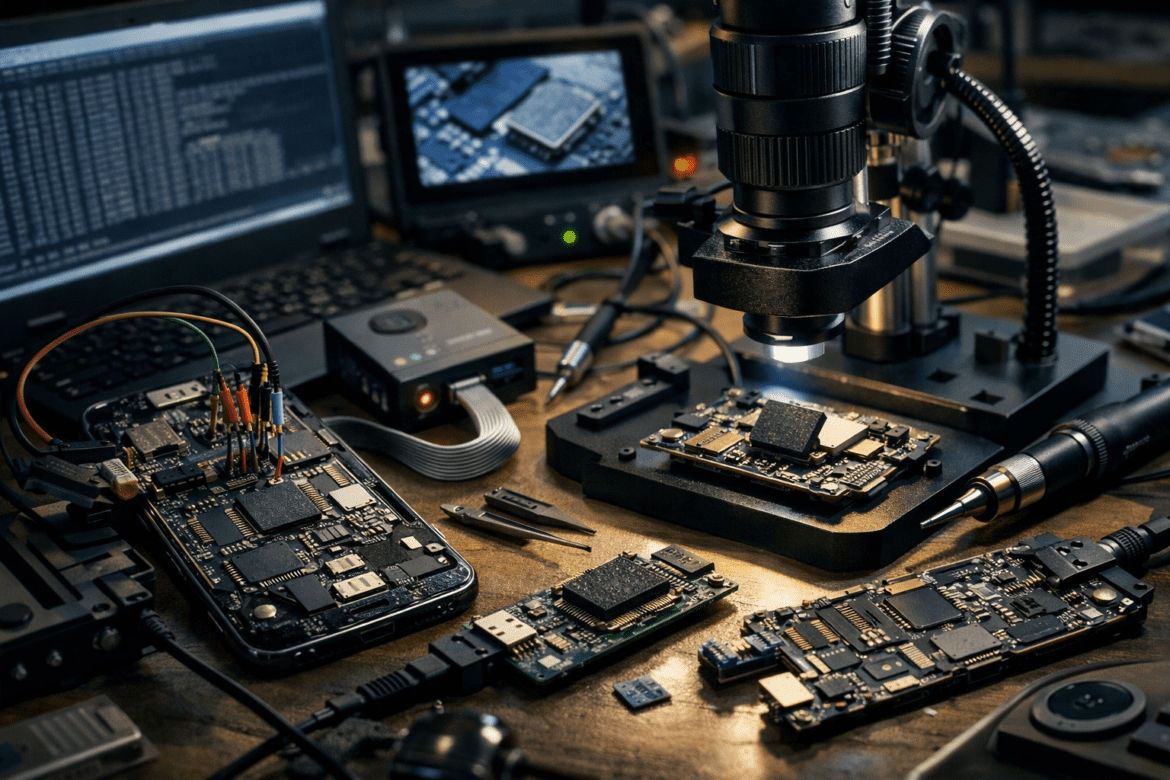
Advanced Mobile Forensics: JTAG, Chip-Off, and ISP Extraction
Modern smartphones store vast amounts of digital evidence, including messages, call logs, photos, application data, and system artifacts. As a result, mobile devices often become critical sources of information during digital investigations. However, investigators do not always gain easy access to this data. In many cases, devices may be locked, ...