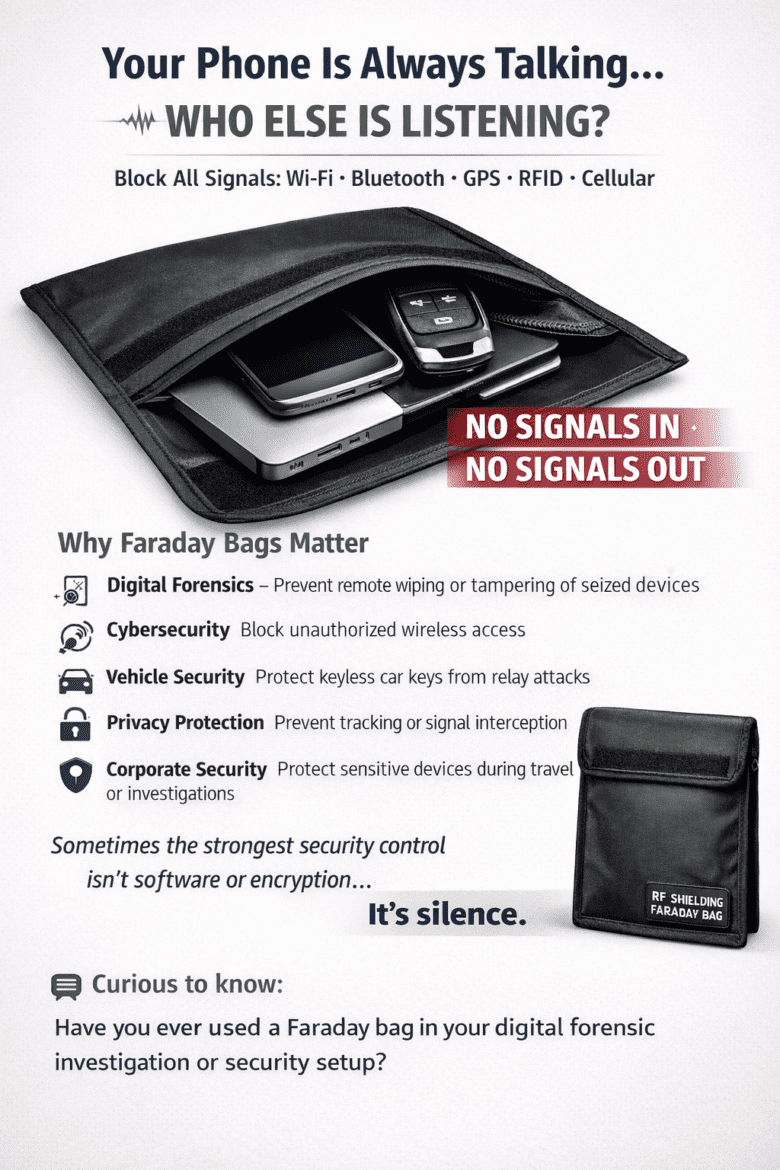
Faraday Bags: Importance of Protecting Digital Privacy and Device Security
Faraday Bags: Importance of Protecting Digital Privacy and Device Security The Faraday bags importance has grown significantly in today’s connected world. Smartphones, car keys, credit cards, and passports constantly send and receive wireless signals. These signals make everyday tasks easier, but they also create opportunities for hacking, tracking, and data ...