Introduction
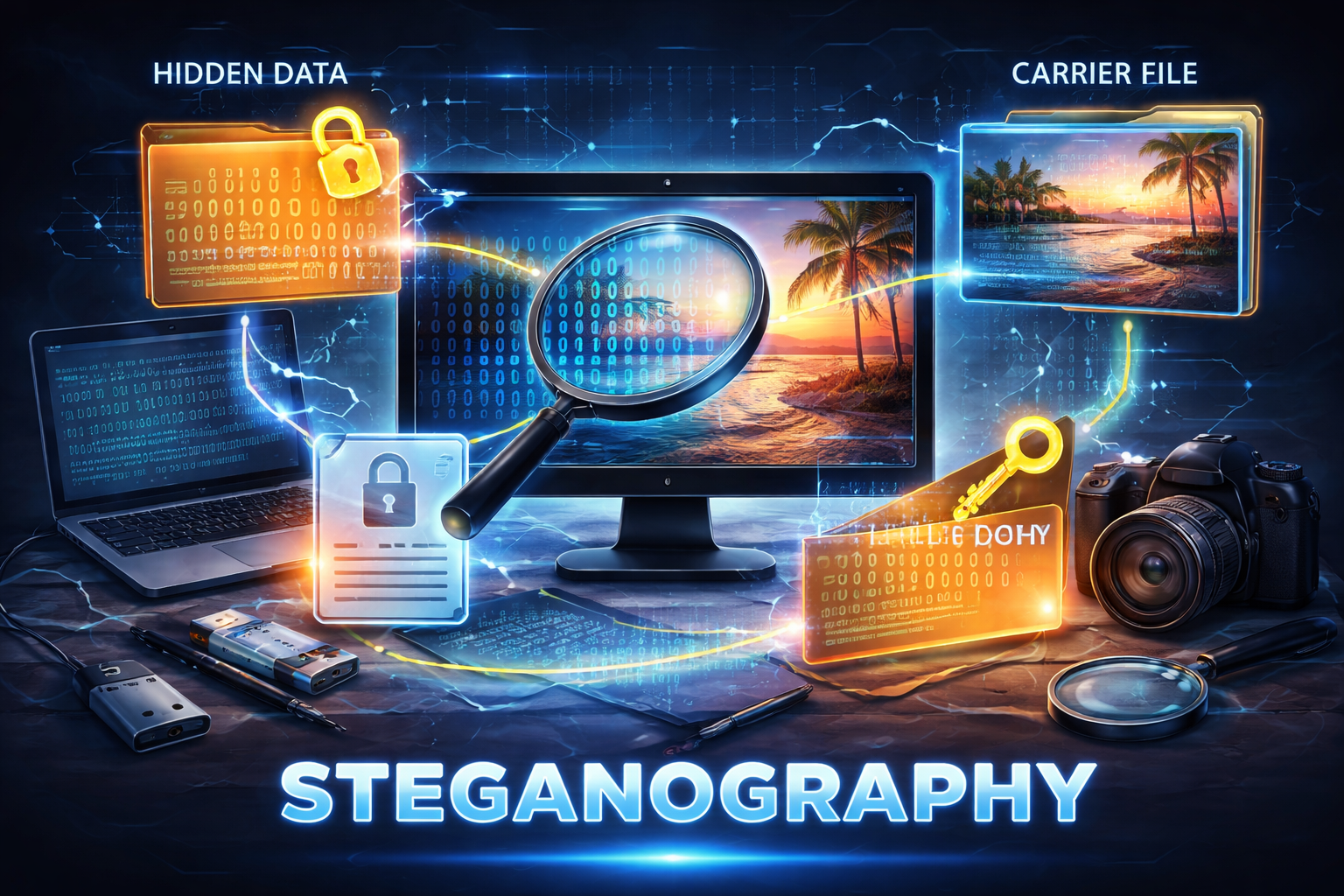
In the world of cybersecurity and digital forensics, hiding information is just as important as protecting it. This is where steganography comes into play. It is a technique used to conceal secret data within ordinary files such as images, audio, or videos.
As cyber threats evolve, steganography is increasingly being used by attackers to hide malicious data. Therefore, understanding how it works is essential for both cybersecurity professionals and forensic investigators.
What is Steganography?
Steganography is the practice of hiding confidential information inside another file so that it remains invisible to the human eye. In simple terms, it is different from encryption because it conceals the existence of the data itself.
For example, a secret message can be embedded within an image without changing its visible appearance.
Types of Steganography
Image Steganography
First of all, image steganography is the most common type. Data is hidden within pixel values, often using techniques like Least Significant Bit (LSB).
Audio Steganography
Next, audio files are used to embed hidden messages by modifying sound waves.
Video Steganography
Additionally, videos allow large amounts of data to be hidden across multiple frames.
Text Steganography
Finally, hidden messages are inserted within text using spacing, formatting, or character manipulation.
How Steganography Works
Steganography works by embedding secret data into a carrier file. Typically, algorithms modify bits of the original file without significantly altering its appearance or functionality.
As a result, the hidden data remains undetectable unless specialized tools are used.
Steganography in Digital Forensics
In forensic investigations, steganography plays a dual role. On the one hand, criminals use it to hide illegal data. On the other hand, investigators use techniques to detect and extract hidden information.
For instance, forensic experts analyze file structures, metadata, and anomalies to uncover concealed data.
Detection Techniques (Steganalysis)
Statistical Analysis
Firstly, statistical methods identify unusual patterns in files.
File Comparison
Secondly, comparing original and suspected files helps detect hidden changes.
Machine Learning
Moreover, AI-based tools can identify hidden data more efficiently.
Metadata Examination
Finally, metadata analysis reveals inconsistencies that may indicate hidden content.
Advantages of Steganography
- Enhances data confidentiality
- Hides the existence of communication
- Useful for secure data transfer
However, these advantages can also be misused by cybercriminals.
Challenges in Detection
High Complexity
On the one hand, advanced techniques make detection difficult.
Large Data Volume
On the other hand, analyzing large files requires time and resources.
Evolving Methods
Furthermore, new hiding techniques are constantly being developed.
Real-World Applications
Steganography is used in:
- Cybersecurity
- Military communication
- Digital watermarking
- Intellectual property protection
Additionally, it plays a role in secure communication systems.
Conclusion
To sum up, steganography is a powerful technique for hiding information within digital media. While it offers benefits in secure communication, it also poses challenges in digital forensics.
Ultimately, understanding steganography and its detection methods is crucial in combating cybercrime and ensuring data security.



Post comments (0)