How Hackers Leave Digital Footprints and How Investigators Track Them
Cybercrime continues to grow as technology becomes more advanced and widely used. Hackers often attempt to hide their identity while carrying out illegal activities such as data theft, ransomware attacks, and financial fraud. However, even skilled cybercriminals leave behind traces of their actions. These traces are known as digital footprints. Understanding how hackers leave digital footprints and how investigators track them is essential in modern cybercrime investigations. Digital forensic experts analyze these footprints to identify suspects and reconstruct cyberattacks.
Understanding Digital Footprints
Digital footprints refer to the electronic traces that users leave when they interact with computers, networks, or online services. Every action performed on a digital system generates data that can later be analyzed during an investigation.
Hackers may attempt to delete logs or hide their activities, but many digital traces still remain within systems, networks, and devices. Investigators rely on these traces to understand how a cyberattack occurred and who might be responsible.
The process of analyzing such evidence is part of Digital Forensics, a specialized field within Cybersecurity that focuses on identifying and analyzing electronic evidence.
Types of Digital Footprints Left by Hackers
Hackers often leave different types of digital footprints during cyberattacks. These traces help investigators reconstruct the sequence of events.
IP Address Records
One of the most common digital footprints is the Internet Protocol (IP) address. When hackers access a system or website, the network often records the IP address used during the connection.
Although hackers may attempt to hide their IP addresses using VPN services or proxy servers, investigators can still analyze network logs and traffic patterns to identify suspicious connections.
System and Server Logs
Operating systems and servers automatically record user activities in log files. These logs may contain information about login attempts, file access, software installation, and network activity.
Even if hackers delete some logs, investigators may recover them using forensic techniques. These records help experts identify the time, location, and methods used during the attack.
Malware Signatures
Hackers frequently use malicious software to gain unauthorized access to systems. Malware leaves behind unique patterns known as signatures.
Digital forensic investigators analyze malware code to understand how it operates and who might have created it. By comparing malware samples with known cybercrime databases, investigators can sometimes link attacks to specific hacker groups.
Browser and Internet Activity
Hackers often interact with websites or online services while planning or executing cyberattacks. Web browsers record information such as visited websites, cached data, cookies, and download history.
Investigators analyze this data to identify suspicious activities related to hacking attempts or data theft.
How Investigators Track Digital Footprints
Cybercrime investigators use several advanced techniques to track the digital footprints left by hackers. These techniques help experts gather evidence and identify the individuals responsible for cyberattacks.
Network Traffic Analysis
Investigators analyze network traffic to identify unusual patterns or suspicious connections. By studying network data, experts can determine how attackers entered the system and what actions they performed.
Network analysis tools allow investigators to trace connections between devices and identify possible sources of the attack.
Log File Examination
Log file analysis is another important step in tracking hackers. Investigators examine system logs, firewall records, and server logs to reconstruct the timeline of events.
These records often reveal login attempts, unauthorized access, and changes made to files or databases.
Malware Analysis
When hackers use malware during cyberattacks, forensic experts analyze the malicious software to understand its structure and behavior.
This process may involve reverse engineering the malware code to identify its origin, purpose, and communication methods. Malware analysis often helps investigators connect cyberattacks to specific criminal groups.
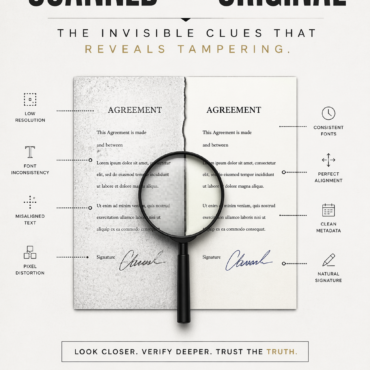
Digital Evidence Correlation
Investigators rarely rely on a single piece of evidence. Instead, they correlate information from multiple sources such as network logs, system files, and digital devices.
By combining these pieces of evidence, investigators create a detailed picture of the cyberattack and identify the responsible individuals.
Many organizations follow cybersecurity guidelines developed by institutions such as the National Institute of Standards and Technology when conducting digital investigations.
Challenges in Tracking Hackers
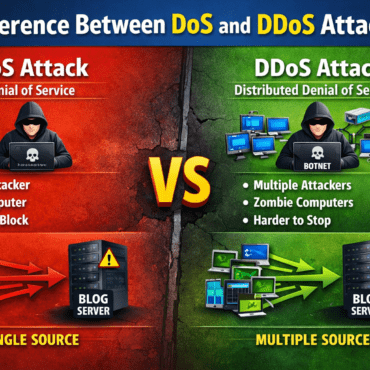
Tracking hackers can be challenging because cybercriminals often use advanced techniques to hide their identity. They may use anonymous networks, encryption, or compromised computers to disguise their location.
For example, some attackers route their internet traffic through multiple servers located in different countries. This process makes it harder for investigators to trace the original source of the attack.
Despite these challenges, digital forensic experts can still uncover valuable evidence by analyzing patterns, technical indicators, and digital artifacts.
Role of Digital Forensics in Cybercrime Investigations
Digital forensics plays a crucial role in identifying and prosecuting cybercriminals. Investigators use specialized software and hardware tools to recover deleted data, analyze system logs, and examine digital devices.
These forensic methods allow experts to gather reliable evidence that can be presented in court. As cybercrime continues to evolve, digital forensic techniques also continue to improve.
Conclusion
Hackers may attempt to hide their identity while conducting cyberattacks, but they almost always leave behind digital footprints. These traces include IP addresses, system logs, malware signatures, and internet activity records.
By analyzing these digital footprints, investigators can track cybercriminals and uncover valuable evidence. Through advanced digital forensic techniques, investigators continue to strengthen cybersecurity and combat cybercrime effectively.


Post comments (0)