How Investigators Track Criminals on the Dark Web
The internet has become an essential part of modern life, but it also provides opportunities for criminal activities. One of the most mysterious parts of the internet is the dark web, a hidden section of the internet that cannot be accessed through standard search engines like Google or Bing. While the dark web is often associated with illegal activities, it is also used by journalists, activists, and people who want to maintain privacy online. However, criminals sometimes use it to hide their identities and conduct illegal transactions. Despite this anonymity, investigators have developed advanced methods to track criminals operating on the dark web.
What Is the Dark Web?
The dark web is a small portion of the internet that requires special software to access. The most common tool used to browse the dark web is the Tor (The Onion Router) network, which hides users’ identities by routing internet traffic through multiple servers around the world. This process makes it difficult to trace the origin of online activities.
Because of this anonymity, the dark web has become a place where illegal goods and services are sometimes traded. These may include stolen data, illegal drugs, hacking tools, counterfeit documents, and other unlawful items. Criminal marketplaces and forums on the dark web allow users to communicate and conduct transactions while attempting to remain anonymous.
Challenges for Investigators
Tracking criminals on the dark web is not easy. The primary challenge is anonymity. Tools like Tor hide a user’s IP address, which normally helps investigators identify the location of a person online. Additionally, many dark web users rely on cryptocurrencies such as Bitcoin for transactions, which can make financial tracking more complicated.
Criminals also use encrypted communication platforms, fake identities, and secure servers to avoid detection. These techniques create multiple layers of protection, making investigations more complex than traditional cybercrime cases.
Digital Forensics and Cyber Investigation
Despite these challenges, investigators use digital forensics techniques to uncover evidence on the dark web. Digital forensics involves collecting, analyzing, and preserving digital data to identify criminal activities.
Forensic experts examine devices such as computers, smartphones, and storage drives that may contain traces of dark web activity. Even if criminals try to delete files or browsing history, investigators can often recover hidden or deleted data using specialized tools.
Digital evidence such as login records, communication logs, and downloaded files can reveal valuable clues about a suspect’s activities.
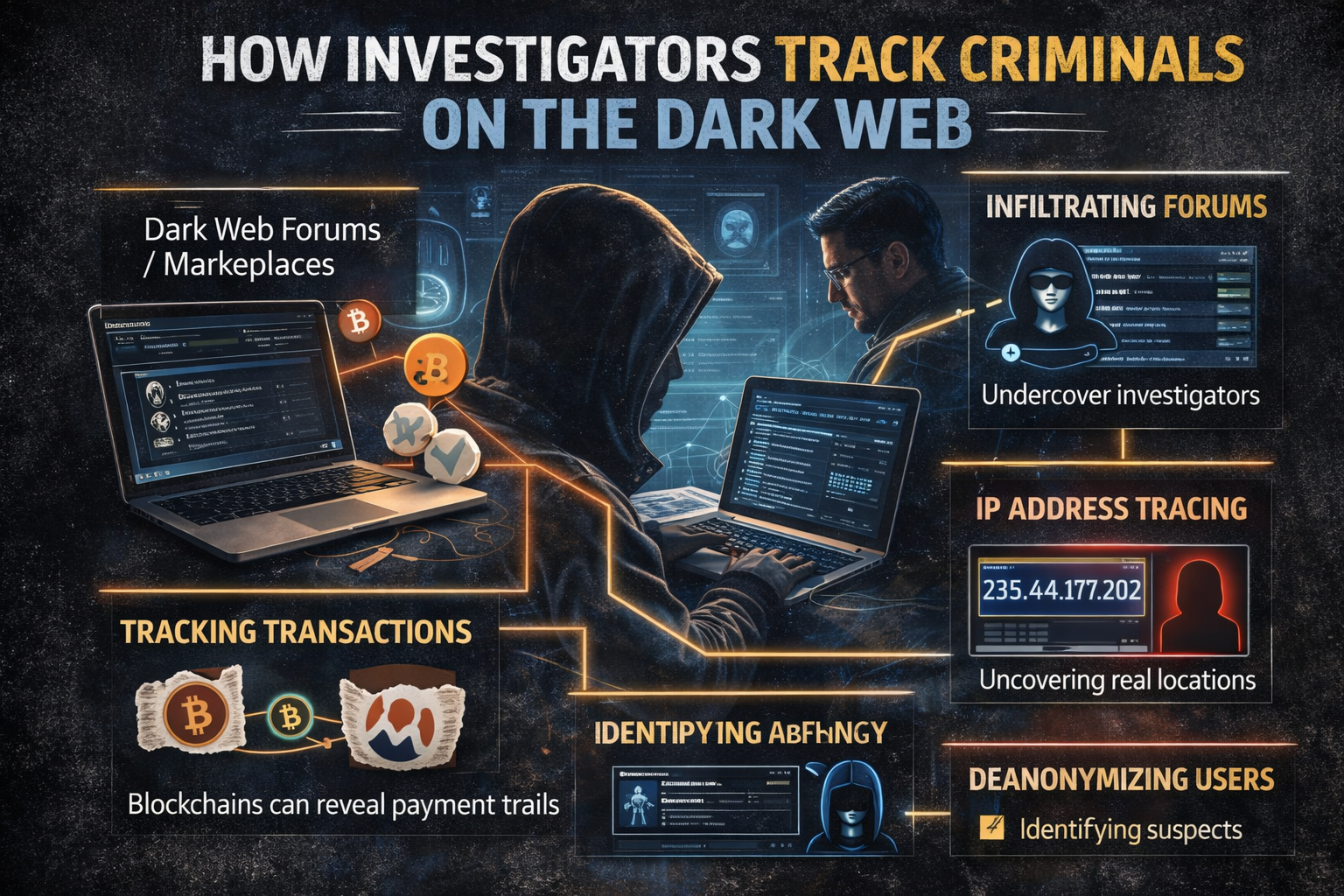
Undercover Operations
Another common strategy used by law enforcement is undercover investigation. Investigators may create fake identities and join dark web marketplaces or forums to observe criminal activities. By interacting with suspects, they can gather information about illegal networks, payment methods, and distribution channels.
Undercover operations help investigators understand how criminal organizations operate. In some cases, authorities have even taken control of dark web marketplaces and monitored user activity to identify thousands of criminals.
Tracking Cryptocurrency Transactions
Many dark web transactions involve cryptocurrencies, which are often believed to be completely anonymous. However, most cryptocurrencies operate on blockchain technology, which records every transaction in a public ledger.
Investigators use blockchain analysis tools to track cryptocurrency movements. By analyzing transaction patterns and linking them to known wallet addresses, investigators can sometimes identify the individuals behind illegal payments.
In some cases, criminals make mistakes, such as transferring cryptocurrency to exchanges that require identity verification. These mistakes can help investigators connect online activity to real-world identities.
Network Analysis and Traffic Monitoring
Cyber investigators also use network analysis techniques to identify suspicious activities. By studying internet traffic patterns and server connections, experts may find weaknesses in the systems criminals use to hide their identities.
Sometimes law enforcement agencies collaborate with internet service providers, cybersecurity experts, and international organizations to trace criminal networks operating across multiple countries.
Advanced technologies such as artificial intelligence and machine learning are also being used to detect unusual patterns in online activities. These technologies help investigators analyze large amounts of data quickly and identify potential threats.
Human Error and Digital Footprints
Even though the dark web provides anonymity, criminals often make mistakes that expose their identities. For example, they might reuse usernames, passwords, or email addresses that are linked to their real identities on other websites.
Some criminals accidentally reveal personal details during online conversations or leave digital footprints that investigators can follow. These small mistakes can provide crucial leads that help authorities track suspects.
International Cooperation
Cybercrime investigations often require cooperation between different countries because dark web activities can involve servers, users, and transactions from multiple locations around the world. Law enforcement agencies work together through international organizations and information-sharing networks.
Joint operations have successfully shut down several major dark web marketplaces and arrested many individuals involved in illegal activities.
The Importance of Digital Forensics
Digital forensics plays a critical role in tracking criminals on the dark web. By combining technical expertise, investigative techniques, and advanced technology, investigators can uncover hidden evidence and identify suspects.
As cybercrime continues to evolve, digital forensic experts are constantly developing new tools and methods to keep up with criminals who attempt to hide online.
Conclusion
Although the dark web is designed to provide anonymity, it does not make users completely invisible. Investigators use a combination of digital forensics, undercover operations, blockchain analysis, and international cooperation to track criminals operating in hidden online networks.
Criminals often believe they are safe behind layers of encryption and anonymous browsing tools. However, even the smallest mistake or digital trace can lead investigators to uncover their identities. As technology continues to advance, law enforcement agencies are becoming more effective at detecting and preventing illegal activities on the dark web, ensuring that cyberspace becomes safer for everyone.

Post comments (0)