Introduction
A single error can permanently damage the integrity of digital evidence in forensic investigations. Digital evidence plays a crucial role in both criminal and civil cases, helping investigators reconstruct events and establish facts.
However, unlike physical evidence, digital data is extremely fragile. Improper handling—even unintentionally—can destroy its forensic value forever. Therefore, understanding how to preserve digital evidence integrity is essential.
Why Digital Evidence Is So Fragile
Many assume digital data is stable, but in reality, it changes constantly.
Digital evidence:
- Updates automatically
- Records background activity
- Alters metadata silently
- Can overwrite deleted data
Even simple actions can compromise forensic data preservation.
The Critical Mistake: Improper Device Access
The most damaging mistake is accessing a device without proper forensic procedures.
Common examples:
- Turning on a seized computer
- Connecting a drive to a personal system
- Opening files without safeguards
- Taking screenshots instead of acquiring data
These actions immediately affect digital evidence integrity.
What Gets Destroyed During Improper Access
1. Metadata Alteration
Opening files changes:
- Access timestamps
- Modification dates
- File system records
This disrupts timelines critical to investigations.
2. Loss of System Artifacts
Operating systems generate logs and temporary files.
Improper access may overwrite:
- Browser history
- Cache data
- Application logs
These artefacts often contain key evidence.
3. Permanent Loss of Deleted Data
Deleted files remain recoverable until overwritten.
Improper access can overwrite the data permanently, making recovery impossible.
Why Copy-Pasting Is Not Forensic Acquisition
Normal file copying does NOT preserve the following:
- Hidden files
- Deleted data
- Slack space
- File system structure
Additionally, it lacks verification using a cryptographic hash function.
Without hashing, evidence cannot be proven authentic in court.
Legal Consequences of Mishandling Digital Evidence
Courts require:
- Integrity
- Authenticity
- Proper chain of custody
If mishandled:
- Evidence may be challenged
- Chain of custody weakens
- Data may be excluded
Even strong cases can fail due to poor handling.
How Experts Protect Digital Evidence Integrity
1. Forensic Acquisition
Experts create a forensic image by capturing it bit by bit:
- All data (visible + hidden)
- Deleted files
- Unallocated space
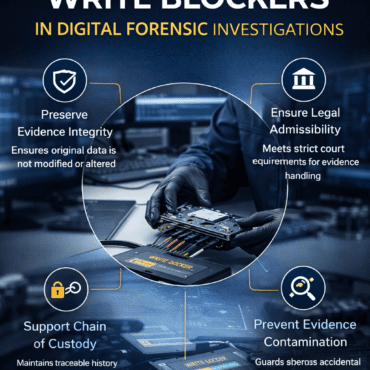
2. Use of Write Blockers
Write blockers prevent changes to the original device.
This ensures safe evidence handling.
3. Hash Verification
Hash values (MD5, SHA-256) confirm data integrity.
Matching hashes prove the evidence is unchanged.
Why This Mistake Happens So Often
Common reasons include:
- Lack of forensic training
- Urgency at crime scenes
- Misunderstanding of digital evidence
- Assumption that “viewing is harmless”
In reality, even minimal interaction can cause damage.
The Reality of Digital Evidence Handling
Digital evidence does not get destroyed on its own—it is damaged by improper handling.
Oncece altered, the original state can NEVER be restored.
Conclusion
The most significant mistake that destroys digital evidence forever is improper access before forensic acquisition.
To maintain digital evidence integrity, evidence must be:
- Untouched
- Verified
- Legally defensible



Post comments (0)