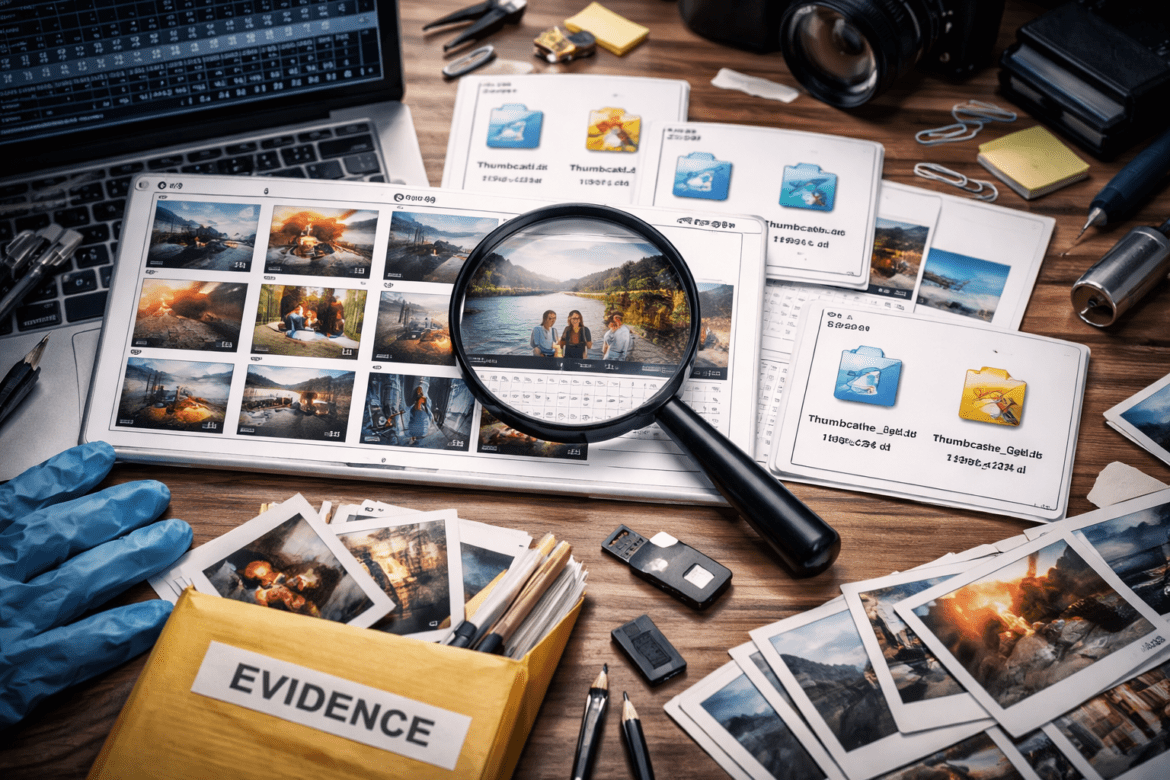
Thumbcache Files and Image Evidence in Digital Forensics
Introduction In the modern digital world, images play a crucial role in communication, documentation, and personal expression. From photographs captured on smartphones to screenshots stored on computers, image files are frequently encountered during digital forensic investigations. However, even when a user deletes or moves image files, traces of those images ...