AI vs Digital Forensics: Can Artificial Intelligence Outsmart Investigators?
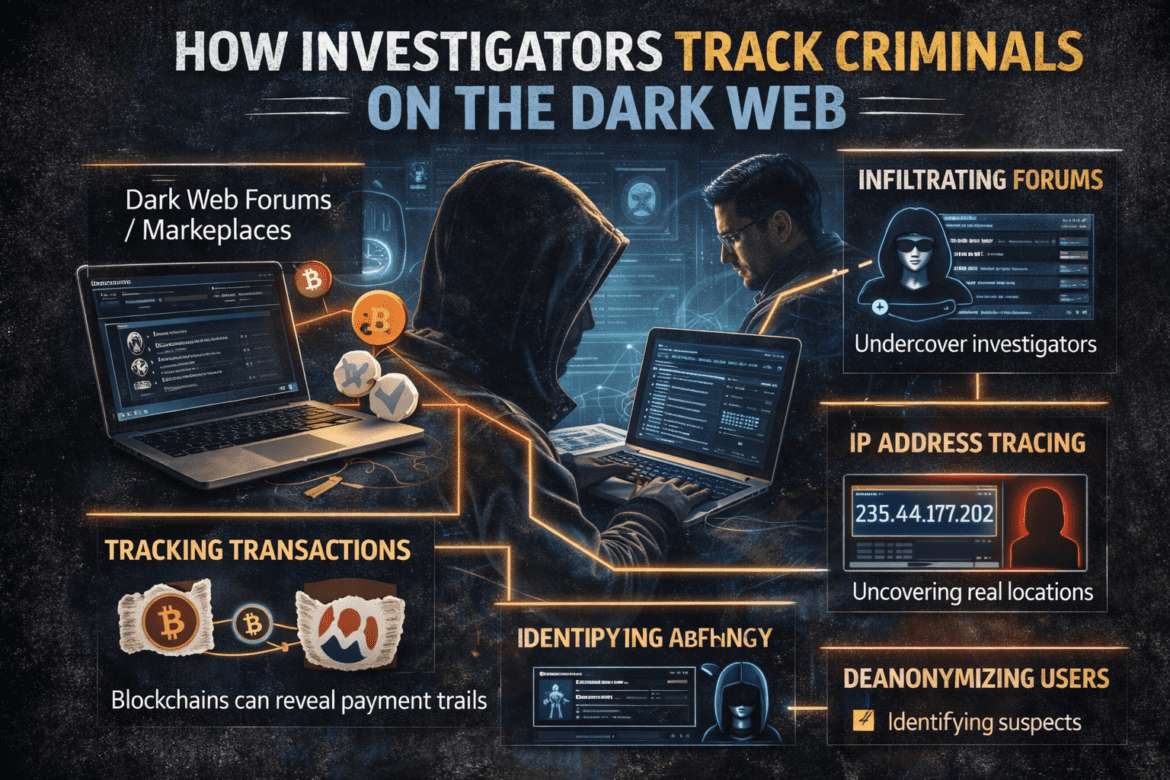
Introduction The debate around AI vs. digital forensics is becoming more relevant as technology evolves rapidly. On one hand, artificial intelligence is helping investigators solve complex cases faster. On the other hand, cybercriminals are also using AI to create advanced attacks and hide evidence. So, can AI outsmart digital forensic ...