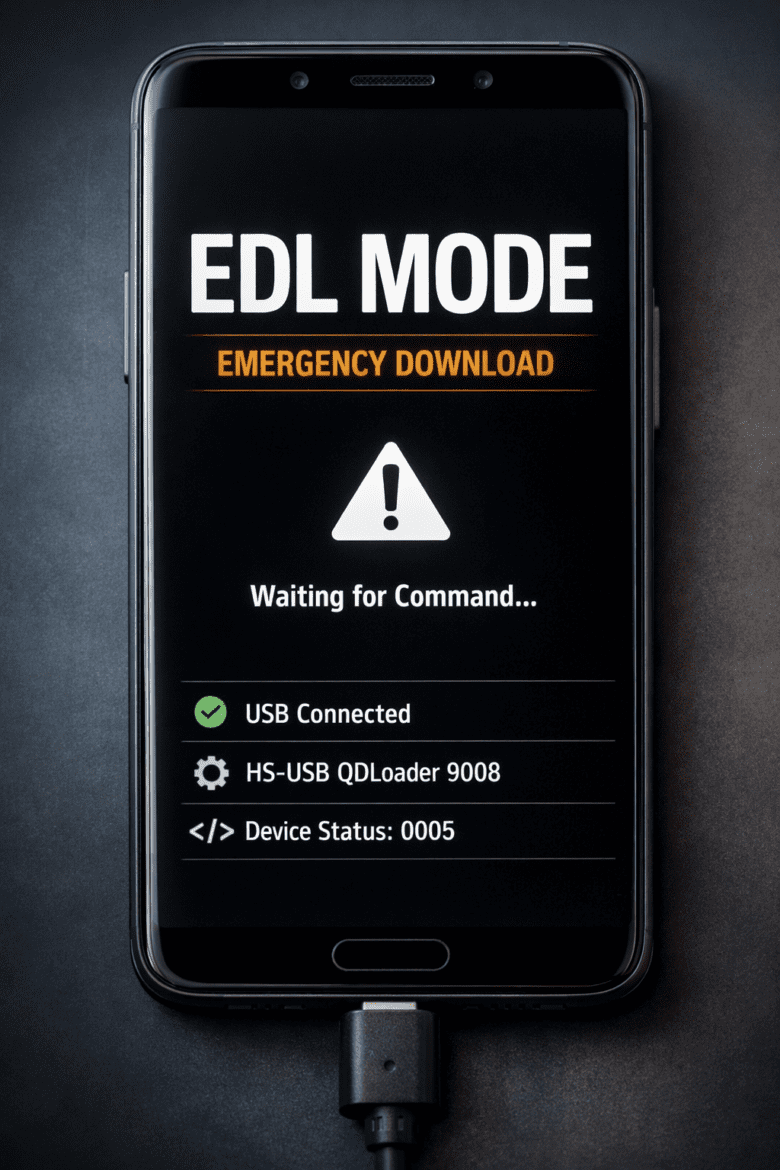
What is EDL Mode? A Guide to Emergency Download Mode in Smartphones
What is EDL Mode? A Guide to Emergency Download Mode in Smartphones Smartphones store a large amount of personal and professional data. Messages, photos, apps, and documents all exist on a single device. When a phone stops working or fails to boot, recovering that data becomes difficult. EDL Mode, also ...