Introduction
In today’s digital era, mobile phones are the primary repositories of personal and professional information. From conversations and emails to financial records and multimedia data, smartphones often hold evidence crucial to legal investigations. However, one of the biggest challenges faced by digital forensic experts is gaining access to locked devices. With increasing security measures such as PINs, passwords, patterns, biometric locks, and encryption, bypassing mobile locks has become both complex and critical in forensic examinations.
Forensic professionals cannot rely on trial-and-error techniques or brute-force attempts that may damage the device or alter the data. Instead, they employ specialized forensic tools and methodologies designed to safely bypass locks and extract data without compromising its integrity.
Why Mobile Lock Bypass is Needed
Mobile lock bypass is commonly required in scenarios such as:
-
Criminal Investigations – Accessing messages, call logs, or location data to build a case.
-
Corporate Cases – Uncovering insider threats, data theft, or policy violations.
-
Cybercrime Forensics – Collecting evidence of online fraud, hacking attempts, or social engineering attacks.
-
Civil Disputes – Resolving matters related to family law, financial disputes, or harassment cases.
In all these cases, bypassing locks must be done lawfully, ensuring data integrity for its admissibility in court.
Common Lock Types on Mobile Devices
Modern smartphones employ multiple locking mechanisms, such as:
-
PIN and Passwords – Numeric or alphanumeric locks.
-
Pattern Locks – Connect-the-dots style authentication.
-
Biometric Locks – Fingerprint, facial recognition, or iris scan.
-
Encryption – Full-disk encryption adds another layer of security beyond screen locks.
Each lock type requires different forensic approaches and tools.
Forensic Tools Used for Mobile Lock Bypass
1. Cellebrite UFED (Universal Forensic Extraction Device)
One of the most popular tools among law enforcement agencies. It supports advanced lock bypass techniques including:
-
Bypassing PIN, pattern, and password locks.
-
Exploiting vulnerabilities in specific device models.
-
Extracting encrypted data without damaging its integrity.
2. Magnet AXIOM & Magnet GRAYKEY Integration
GrayKey, widely used for iOS devices, allows brute-force unlocking in a controlled forensic environment. When integrated with Magnet AXIOM, it enables complete evidence extraction and analysis.
3. MSAB XRY
XRY is another reliable forensic toolset that offers mobile unlocking capabilities, especially for older devices or certain Android models. It ensures chain-of-custody compliance and safe data handling.
4. Oxygen Forensic Detective
This tool combines lock bypass methods with cloud extraction. It supports a variety of devices and can retrieve valuable artifacts even if full bypass is not possible.
5. MOBILedit Forensic
Known for its compatibility with multiple devices, MOBILedit provides options for bypassing screen locks, analyzing SIM cards, and performing advanced searches across extracted data.
Methods of Mobile Lock Bypass
1. Exploiting Software Vulnerabilities
Some forensic tools use zero-day or known vulnerabilities to bypass locks. These methods are non-destructive and maintain data authenticity.
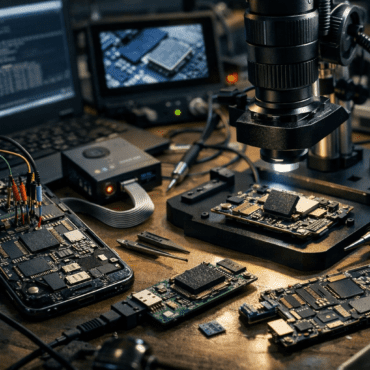
2. Chip-Off and JTAG Analysis
When traditional bypass fails, hardware-based approaches are used:
These methods require high expertise but can recover data even from severely locked or damaged devices.
3. Brute-Force in Controlled Environment
Unlike random guesswork, forensic brute-forcing is systematic and ensures no data alteration. Tools like GrayKey specialize in this method for iPhones.
4. Cloud Data Extraction
If the device is encrypted, forensic experts may bypass the lock by retrieving synced data from associated cloud accounts, provided they have legal authorization.
5. SIM and Backup Analysis
In cases where direct bypass is difficult, investigators may recover critical evidence from SIM cards, memory cards, or backup files stored on computers or cloud services.
Tips for Mobile Lock Bypass in Forensic Practice
-
Maintain Legal Authorization – Ensure all bypass attempts are backed by court orders or legal permissions.
-
Use Certified Tools – Employ industry-recognized forensic tools that comply with evidentiary standards.
-
Work on a Forensic Image – Always create a bit-by-bit copy before attempting bypass to preserve original evidence.
-
Avoid Data Alteration – Never use conventional hacks or third-party unlocking services that compromise evidence integrity.
-
Document Every Step – Maintain chain-of-custody and detailed logs of methods and tools used.
Challenges in Mobile Lock Bypass
-
Advanced Encryption in modern smartphones like iPhone with Secure Enclave.
-
Regular Security Updates patching known vulnerabilities.
-
Device-Specific Variations making universal solutions difficult.
-
Legal & Ethical Concerns surrounding privacy and admissibility of evidence.
Conclusion
Mobile lock bypass is one of the most challenging yet essential aspects of mobile forensic investigations. With the right forensic tools and methods, investigators can lawfully access locked devices while ensuring that evidence remains intact and admissible in court. Whether through software exploits, hardware methods like chip-off, or cloud extractions, the goal remains the same – uncovering the truth while maintaining the highest standards of forensic integrity.
Forensic experts must keep themselves updated with evolving mobile security technologies and continuously refine their techniques. In this ever-changing landscape, mobile lock bypass is not just about unlocking a device—it’s about unlocking the truth.



Post comments (0)