File Signature Analysis: Identifying Files Beyond Extensions
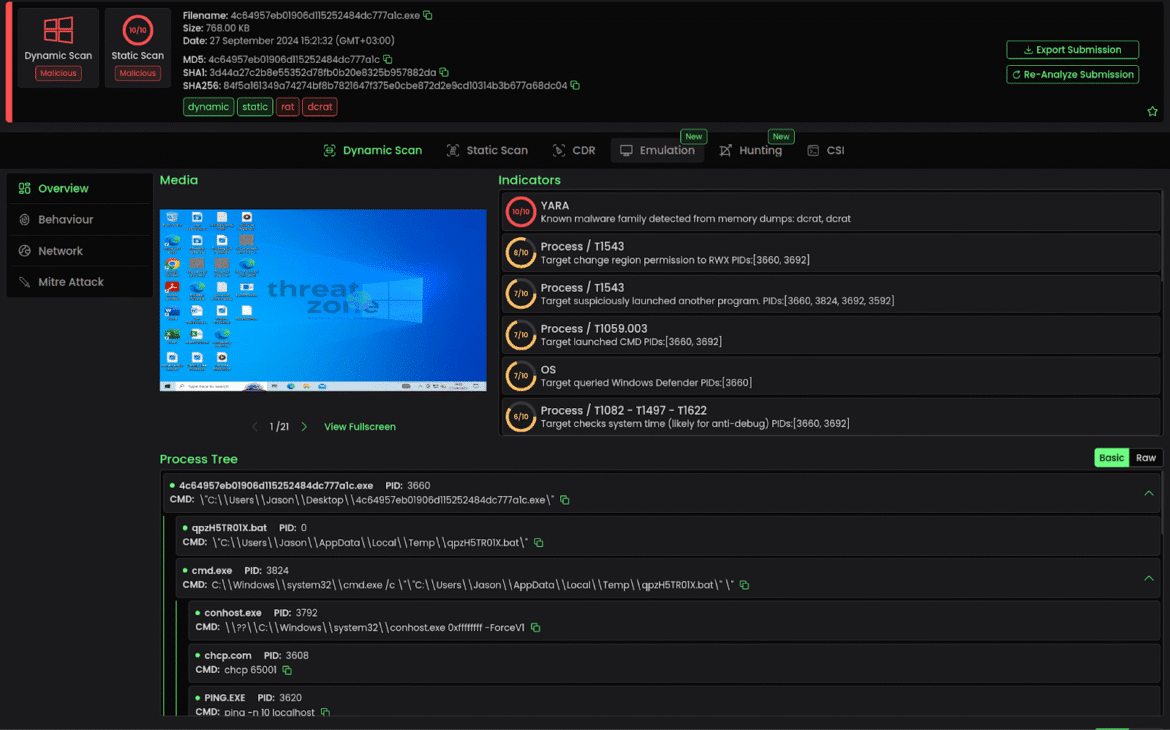
Introduction At first glance, a file extension may seem trustworthy. However, in digital investigations, appearances can be misleading. For example, a file named invoice.pdf might not be a PDF at all. Cybercriminals often rename malicious files to trick users and bypass security filters. As a result, investigators cannot rely only ...