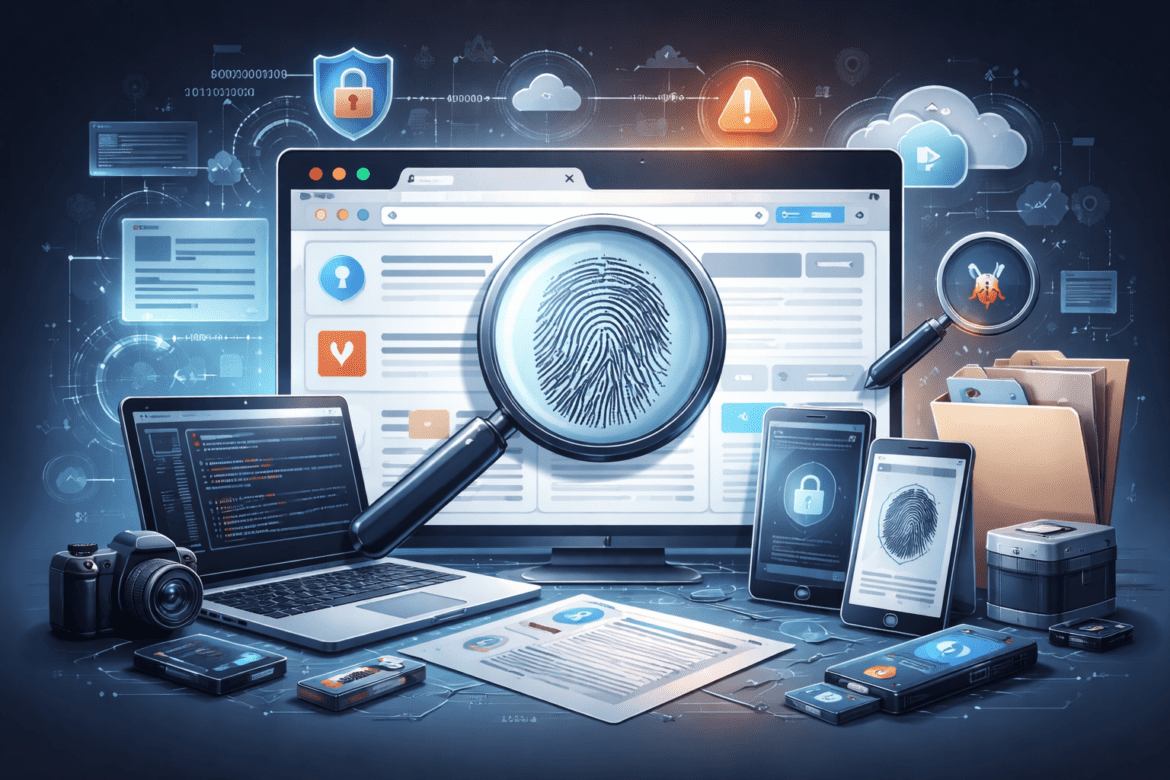
Browser Forensics: Recovering User Activity from Chrome and Edge
Modern investigations often reveal a simple truth: a large portion of user activity happens inside a web browser. From communication and financial transactions to research and file downloads, browsers store valuable traces of user behavior. For digital forensic investigators, browsers such as Google Chrome and Microsoft Edge can provide a detailed record of ...