Introduction
In today’s digital-first world, cybercrime investigations depend heavily on digital forensics. From recovering deleted files to analyzing malware behavior, forensic experts ensure that no digital footprint goes unnoticed.
But criminals are fighting back. They use anti-forensic techniques—methods designed to erase, alter, or hide evidence from investigators. These tactics complicate legal cases, delay justice, and in some instances, make evidence inadmissible in court.
This blog explores the world of anti-forensics, its categories, tools, real-world examples, and how forensic experts counter these techniques to bring criminals to justice.
What is Anti-Forensics?
Anti-forensics refers to a set of deliberate strategies to obstruct forensic investigation. The goals include:
-
Hiding activities (using encryption or steganography)
-
Erasing traces (using wiping tools or file corruption)
-
Manipulating evidence (through timestomping or fake logs)
-
Confusing investigators (planting false evidence)
In essence, anti-forensics is the dark twin of digital forensics, where attackers seek to outsmart investigators.
Categories of Anti-Forensic Techniques
1. Data Hiding
-
Steganography – Concealing text or files inside images, audio, or video.
-
Alternate Data Streams (ADS) – A hidden feature in NTFS file systems to store extra data without showing size changes.
-
Encryption – Using tools like VeraCrypt to lock files beyond forensic access.
-
Password Protection – Locking folders with strong passcodes to buy time.
Example: In corporate espionage cases, trade secrets have been smuggled out hidden inside innocuous image files.
2. Data Destruction
-
File Wiping Tools – Eraser, CCleaner, or DBAN overwrite files multiple times.
-
Disk Formatting/Repartitioning – Wipes metadata and makes recovery harder.
-
Secure Delete Commands – Shred and rm -rf (Linux) used to delete without trace.
-
Wiping Free Space – Overwrites “empty” storage sectors.
Example: In fraud cases, suspects often wipe drives minutes before seizure, but advanced carving can still extract remnants.
3. Data Obfuscation & Manipulation
-
Timestomping – Modifying created/modified/accessed timestamps.
-
Log Tampering – Erasing login/logout records to hide access.
-
Metadata Forgery – Altering EXIF data in images (e.g., changing GPS location).
-
Fake Evidence Planting – Inserting misleading data to frame others.
Example: Hacktivists have been known to timestomp malware files to make them appear older, diverting suspicion.
4. Trail Obfuscation
-
VPNs & TOR – Hide IP addresses and physical location.
-
Proxy Chains – Multiple “hops” to confuse tracing.
-
MAC Spoofing – Masking device identities on networks.
-
Log Flooding – Inserting fake records to bury real evidence.
Example: Ransomware gangs often operate via TOR hidden services, making it nearly impossible to trace origins.
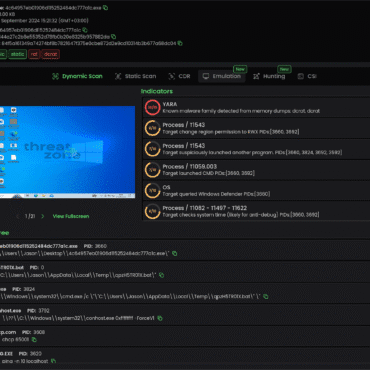
5. Anti-Forensic Malware Techniques
-
Fileless Malware – Lives in RAM only, leaving minimal disk artifacts.
-
Rootkits – Modify OS kernel to hide files, processes, and registry entries.
-
Self-Deleting Malware – Removes itself after execution.
-
Polymorphic Malware – Constantly changes code signatures to avoid detection.
Example: The Stuxnet worm used rootkits to hide its processes, delaying discovery for months.
Tools Commonly Used in Anti-Forensics
-
Encryption: VeraCrypt, BitLocker
-
Wiping: DBAN, CCleaner, Eraser
-
Steganography: Steghide, OpenStego
-
Rootkits: HackerDefender, FU Rootkit
-
Log Cleaners: Evidence Eliminator, Metasploit modules
Impact of Anti-Forensics on Investigations
-
Loss of Critical Evidence – Permanent deletion can cripple cases.
-
False Leads – Fake timestamps/logs waste investigation resources.
-
Delays in Prosecution – Courts require authentic, untampered evidence.
-
Legal Challenges – Manipulated data can make evidence inadmissible.
Countermeasures Against Anti-Forensic Techniques
Forensic experts are not defenseless. Counter-strategies include:
-
Memory Forensics – Tools like Volatility capture RAM to analyze live malware.
-
Timeline Cross-Verification – Comparing logs across systems to detect timestomping.
-
File Carving Tools – Autopsy, EnCase, and X-Ways recover deleted data.
-
Hash Comparisons – Validating file integrity with hash databases.
-
AI & ML Analysis – Detecting anomalies in logs and patterns.
-
Blockchain Evidence Storage – Tamper-proof chains for digital evidence.
-
Network Traffic Monitoring – Tracing activity even if logs are wiped.
Real-World Cases of Anti-Forensics
-
Sony Pictures Hack (2014): Hackers used wipers to destroy servers and hide their trail.
-
APT Groups: Advanced Persistent Threats frequently timestomp and encrypt payloads.
-
Deepfake Investigations: Criminals manipulate metadata to disguise AI-generated content.
Challenges in Combating Anti-Forensics
-
Rapid Evolution of Tools – Criminals adapt faster than laws and forensic methods.
-
Encryption Strength – Breaking modern encryption is nearly impossible without keys.
-
Legal Standards – Proving tampering in court requires airtight methodology.
-
Jurisdiction Issues – Logs/data often spread across international servers.
The Future of Anti-Forensics and Forensics
As cybercriminals refine anti-forensic strategies, forensic experts are adopting AI-driven detection, blockchain-based evidence chains, and advanced live forensics. The cat-and-mouse game will continue—but understanding anti-forensics is the first step to staying ahead.
Conclusion
Anti-forensic techniques represent the hidden battlefield of the cyber world. While they aim to erase, manipulate, or hide digital footprints, forensic experts constantly innovate to counter these methods.
For law enforcement, corporate security teams, and digital forensic professionals, studying anti-forensics is not optional—it is essential. Only by knowing the enemy’s tools can we strengthen defenses, recover hidden evidence, and ensure justice in the digital age.



Post comments (0)