In the world of cybersecurity and digital forensics, malware analysis plays a crucial role in understanding, detecting, and mitigating malicious threats. With thousands of new malware variants emerging daily, investigators and security professionals must use multiple approaches to analyze malicious code effectively.
Two of the most common techniques are Static Malware Analysis and Dynamic Malware Analysis. Each has unique strengths and limitations, and when combined, they provide a more comprehensive understanding of malware behavior.
This blog explores the difference between the two, compares them side by side, and explains why using both approaches together is vital in modern cyber defense and forensic investigations.
What is Static Malware Analysis?
Static Malware Analysis involves examining the malware without executing it. Analysts inspect the code, structure, and binary files to understand the potential behavior.
Techniques Used in Static Analysis:
-
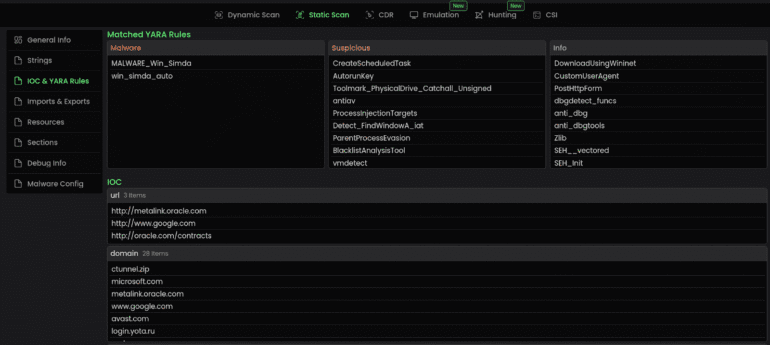
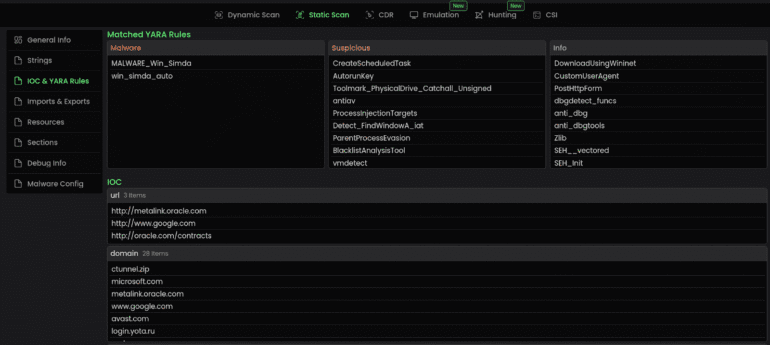
Signature-based detection (hashes, YARA rules)
-
Disassembly & reverse engineering (IDA Pro, Ghidra)
-
String analysis (searching for readable text, URLs, IPs)
-
Header and metadata examination (PE headers, file structure)
✅ Advantages:
-
Safe (since malware is not executed).
-
Quick for identifying known malware families.
-
Provides insights into code logic.
❌ Limitations:
What is Dynamic Malware Analysis?

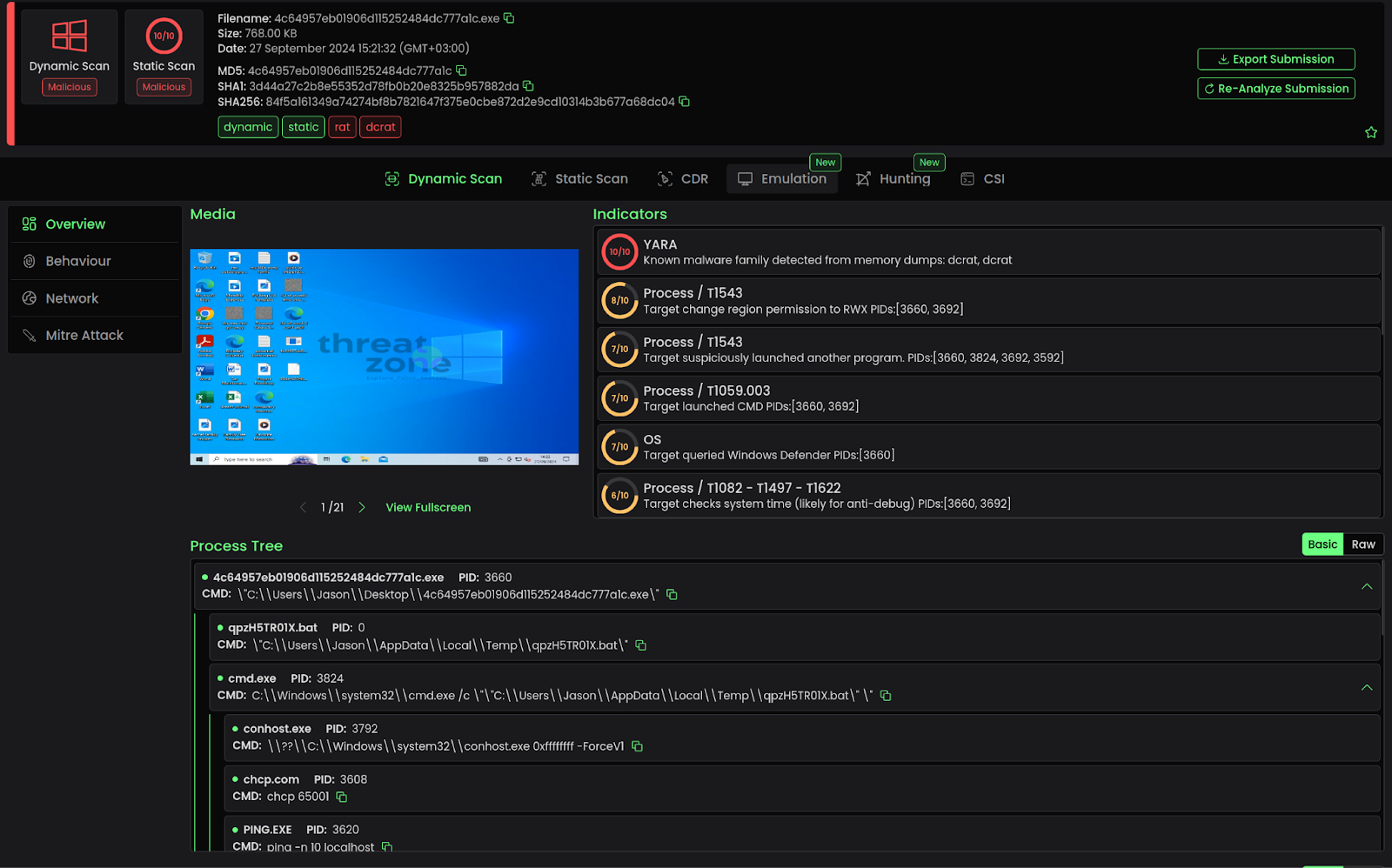
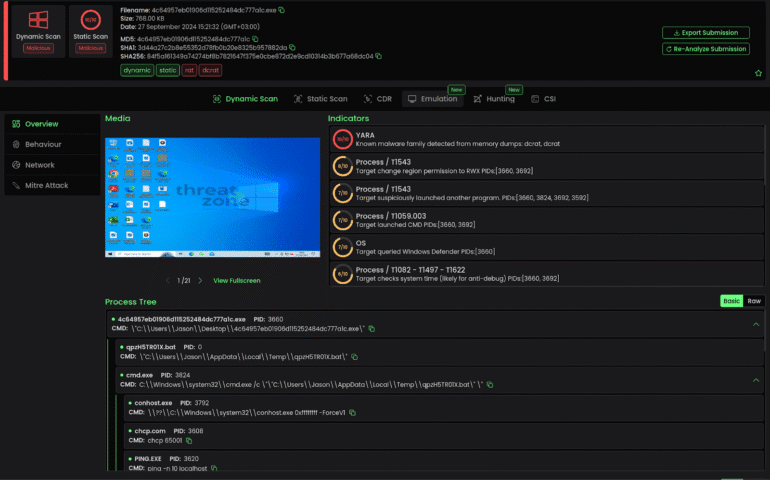
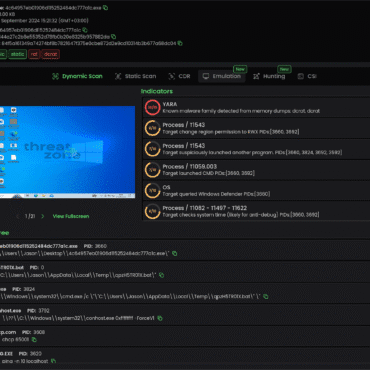
Dynamic Malware Analysis involves executing the malware in a controlled environment (sandbox) to observe its real behavior. This helps identify what the malware actually does when active.
Techniques Used in Dynamic Analysis:
-
Sandbox execution (Cuckoo Sandbox, Any.Run)
-
API call monitoring
-
Registry, file system, and process activity logging
-
Network traffic analysis
✅ Advantages:
-
Reveals real behavior, including obfuscation tricks.
-
Identifies runtime indicators of compromise (IOCs).
-
Helps understand persistence and communication mechanisms.
❌ Limitations:
-
Requires a safe and isolated lab environment.
-
Advanced malware can detect sandboxes and alter behavior.
-
More time-consuming than static analysis.
Comparison Chart – Static vs. Dynamic Malware Analysis
| Aspect |
Static Malware Analysis |
Dynamic Malware Analysis |
| Execution |
Malware is not executed |
Malware is executed in sandbox |
| Safety |
Safer – no runtime risk |
Riskier – requires controlled lab setup |
| Speed |
Faster for known threats |
Slower – needs setup and execution time |
| Detection |
Identifies code-level patterns, signatures |
Observes real-time system changes and behavior |
| Obfuscation Handling |
Struggles with packed/encrypted code |
Can bypass obfuscation by observing runtime output |
| Skill Requirement |
Requires reverse engineering & assembly knowledge |
Easier for beginners (sandbox tools assist) |
| Insights Provided |
Potential behavior (theory of what code can do) |
Actual behavior (what code does do) |
| Use Case |
Early detection, triage, quick classification |
Deep investigation, incident response |
Why Both Are Essential
Neither static nor dynamic analysis alone can provide a complete picture of modern malware. Attackers use sophisticated evasion techniques such as code obfuscation, anti-sandbox checks, and polymorphic code.
-
Static analysis gives analysts a blueprint of the malware. It’s efficient for quick identification and classification.
-
Dynamic analysis reveals the real-world behavior of malware, including hidden payloads and runtime modifications.
When combined:
-
Analysts gain both code-level understanding and execution-level visibility.
-
False negatives are reduced, and hidden features are uncovered.
-
Investigations become stronger, leading to actionable intelligence.
Conclusion
In digital forensics and cybersecurity, relying on just one type of analysis can leave blind spots. Static Malware Analysis helps analysts dissect code without execution, while Dynamic Malware Analysis exposes live behavior.
Together, they create a holistic approach that ensures malware is understood, documented, and mitigated effectively.
At Hawk Eye Forensic, we integrate both static and dynamic malware analysis techniques to uncover even the most advanced threats—providing law enforcement, corporates, and individuals with accurate and reliable digital forensic services.


Post comments (0)