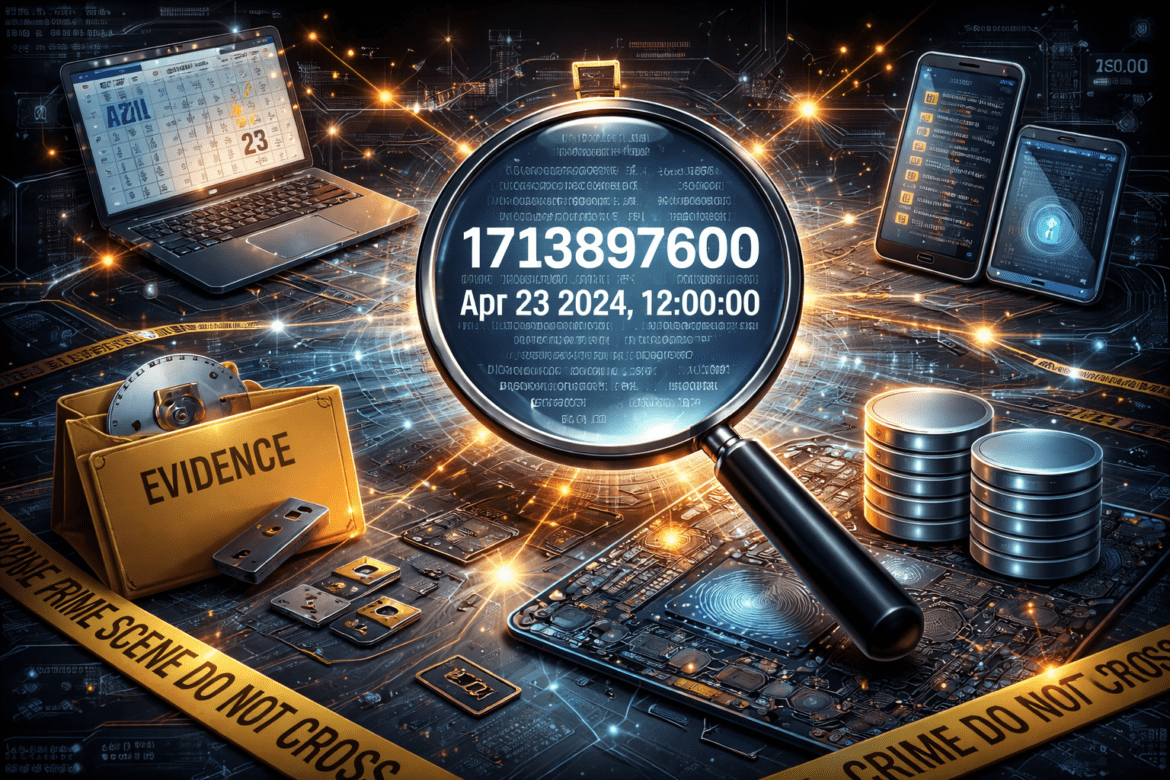
Understanding UNIX Date in Android Devices: What It Means and Why It Matters in Digital Forensics
Introduction If you have ever examined Android logs, mobile extractions, or application databases, you have likely encountered long numbers such as 1708425600. At first glance, these numbers look confusing. However, they represent one of the most important time formats used in digital systems — the UNIX date, also known as ...